What is Host Header Injection?

What is Host Header Injection?
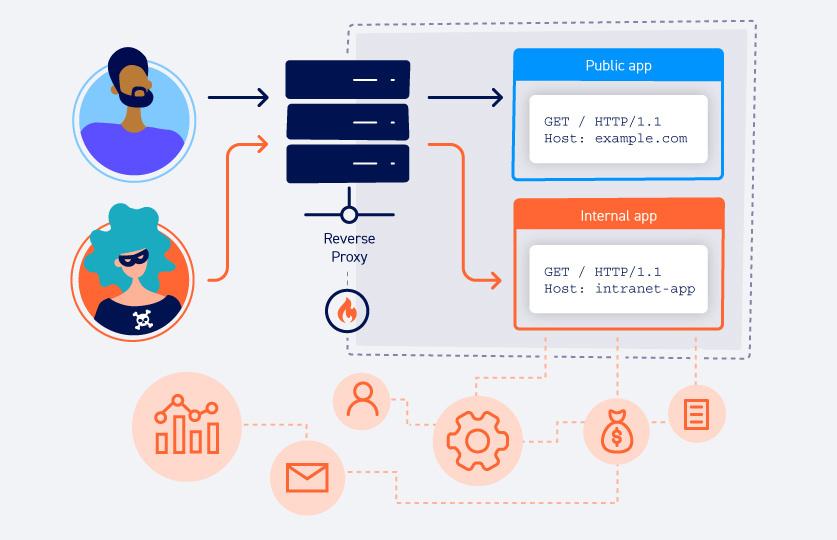
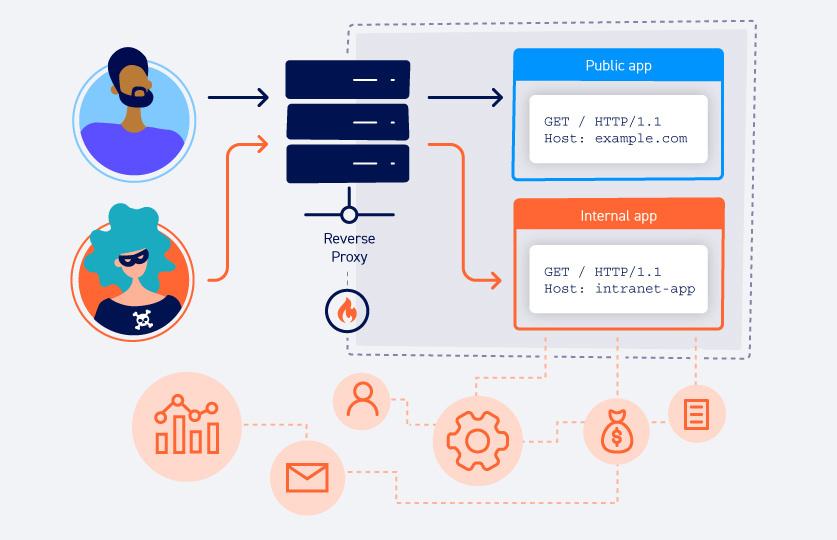
Host Header Injection, also known as Host Header Attack, is a type of attack carried out by manipulating the "Host" header, one of the HTTP headers. When making requests to web applications, situations such as account takeover may occur if the Host header used is changed to an address belonging to the attacker.
How to Detect Host Header Injection Vulnerability?
To detect the host header injection vulnerability in a web application, you can try the following steps in OWASP:
If the phrase "Host: domain.com" in the submitted request is manipulated as "Host: evil.com" and the web application returns 200 OK, there is a vulnerability. To explain with an example;

If the phrase "Host: domain.com" in the submitted request is manipulated as "Host: evil.com" and the web application returns 200 OK, there is a vulnerability. To explain with an example;

Normal Request:
Kod:
POST /page[/SIZE][/COLOR][/B][/I][/CENTER]
[I][B][COLOR=rgb(255, 255, 255)][SIZE=5][CENTER]
Host: www.website.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Referer: https://www.website.com
Origin: https://www.website.com
Alt-Used: www.google.com
Connection: keep-alive
Cookie: 1P_JAR=2021-07-29-20; NID=220=M5Mq4asdasdkA1F3NYIjbczSAD-huTx6zcB0SttHt0Z8Xasdagadsgdsfadasdi4dWaG_Y1e6t2hoJgCbZ37shEeXYK6cAWNZiymLAGa66XjGkOXyJ8ZuV-aL2rwpmoRJqmDsUzL9LSXDq_5k0de-Ns
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: no-cors
Sec-Fetch-Site: same-origin
Content-Length: 0
Manipulated Request:
Kod:
POST /page[/SIZE][/COLOR][/B][/I][/CENTER]
[I][B][COLOR=rgb(255, 255, 255)][SIZE=5][CENTER]
Host: www.evil.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Referer: https://www.website.com
Origin: https://www.website.com
Alt-Used: www.google.com
Connection: keep-alive
Cookie: 1P_JAR=2021-07-29-20; NID=220=M5Mq4asdasdkA1F3NYIjbczSAD-huTx6zcB0SttHt0Z8Xasdagadsgdsfadasdi4dWaG_Y1e6t2hoJgCbZ37shEeXYK6cAWNZiymLAGa66XjGkOXyJ8ZuV-aL2rwpmoRJqmDsUzL9LSXDq_5k0de-Ns
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: no-cors
Sec-Fetch-Site: same-origin
Content-Length: 0If the web application returns 200 OK when "X-Forwarded-Host: evil.com" is added to the sent request, there is a Host Header Injection vulnerability.

Normal Request:
Kod:
POST /page[/B][/I][/SIZE][/COLOR][/CENTER]
[COLOR=rgb(255, 255, 255)][SIZE=5][I][B][CENTER]
Host: www.website.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Referer: https://www.website.com
Origin: https://www.website.com
Alt-Used: www.google.com
Connection: keep-alive
Cookie: 1P_JAR=2021-07-29-20; NID=220=M5Mq4asdasdkA1F3NYIjbczSAD-huTx6zcB0SttHt0Z8Xasdagadsgdsfadasdi4dWaG_Y1e6t2hoJgCbZ37shEeXYK6cAWNZiymLAGa66XjGkOXyJ8ZuV-aL2rwpmoRJqmDsUzL9LSXDq_5k0de-Ns
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: no-cors
Sec-Fetch-Site: same-origin
Content-Length: 0
Manipulated Request:
Kod:
POST /page[/SIZE][/COLOR][/B][/I][/CENTER]
[I][B][COLOR=rgb(255, 255, 255)][SIZE=5][CENTER]
Host: www.website.com
X-Forwarded-Host: www.evil.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Referer: https://www.website.com
Origin: https://www.website.com
Alt-Used: www.google.com
Connection: keep-alive
Cookie: 1P_JAR=2021-07-29-20; NID=220=M5Mq4asdasdkA1F3NYIjbczSAD-huTx6zcB0SttHt0Z8Xasdagadsgdsfadasdi4dWaG_Y1e6t2hoJgCbZ37shEeXYK6cAWNZiymLAGa66XjGkOXyJ8ZuV-aL2rwpmoRJqmDsUzL9LSXDq_5k0de-Ns
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: no-cors
Sec-Fetch-Site: same-origin
Content-Length: 0
How to Fix Host Header Injection Vulnerability? – Precautions
For Nginx and Apache, the request to the page must be checked on a virtual host without being directly ingested into the system. Host and X-Forwarded-Host should ensure that the headers are reliable sources.
Entries from the user must be filtered.

Entries from the user must be filtered.

What Can Be the Effects of Host Header Injection Vulnerability?
As I mentioned at the beginning of our article, Host Header Injection vulnerability is a security vulnerability that can progress to account acquisition. If an attacker raises a server and manages to manipulate the Host HTTP header it sends to the target application, it can intercept other users' password reset tokens.
In addition to this vulnerability, the Insecure Direct Object Reference (IDOR) vulnerability is a high-level security vulnerability that can lead to account takeover.
In addition to this vulnerability, the Insecure Direct Object Reference (IDOR) vulnerability is a high-level security vulnerability that can lead to account takeover.