Welcome Dear TurkHackTeam Members, today I will talk about one of my favorite attacks: XSS.
In every website I enter, I try XSS Payloads to an input place. Just curiosity. So what's XSS?
Cross-site scripting is one of the most common and well known vulnerabilities contained within web applications. It every year appears in the OWASP list of the Top Web Application Security Risks. According to some pages, XSS vulnerabilities are the most common vulnerability type discovered in bug bounty programs, despite the fact that most companies undervalue it because it rarely leads to large-scale data breaches.

The root cause of XSS vulnerabilities is when a web application uses untrusted input without performing proper validation first. If a web server embeds user input in a pages HTML code before sending it to the client, then malicious input could enable the execution of attacker-controlled code within the users browser. You need to filter inputs to prevent these attacks.
The reason for this is that the HTML standard allows other types of code to be embedded in HTML files if they are properly tagged. This includes Javascript code if it is contained within <script></script> tags. If an attacker provides malicious input that results in a valid web page when embedded in the HTML file, then the browser requesting the page will run the code believing that it is a legitimate part of the web page.
Different Types Of XSS
Most used types are Reflected XSS and Persistent, Stored XSS Attacks
Reflected XSS Attacks
Reflected attacks are those where the injected script is reflected off the web server, such as in an error message, search result, or any other response that includes some or all of the input sent to the server as part of the request. Reflected attacks are delivered to victims via another route, such as in an e-mail message, or on some other website.
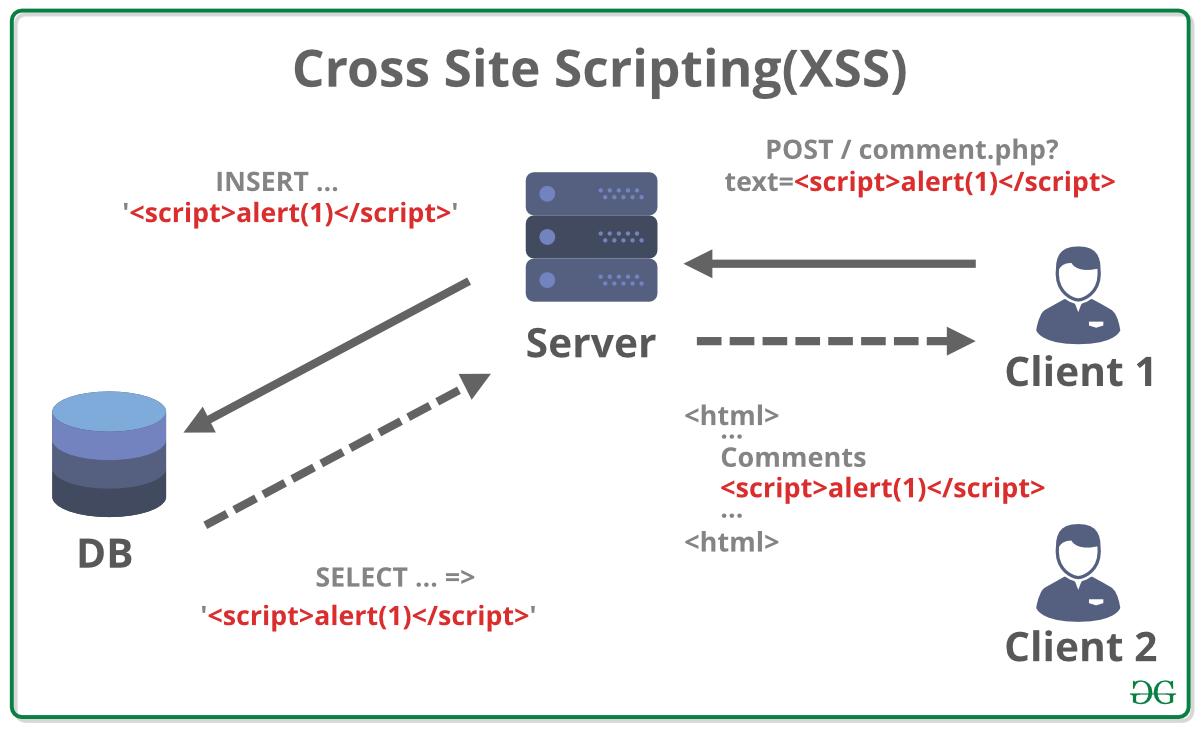
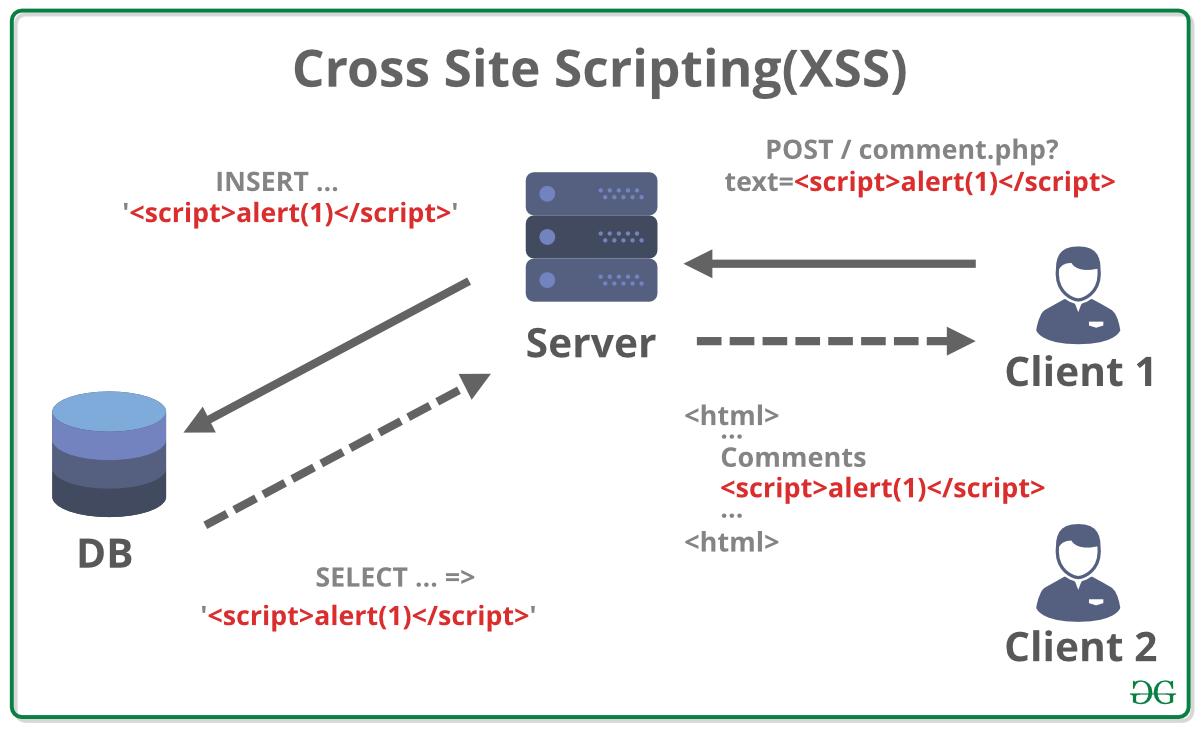
Persistent XSS Attack
Persistent attacks are those where the injected script is permanently stored on the target servers, such as in a database, in a message forum, visitor log, comment field, etc. The victim then retrieves the malicious script from the server when it requests the stored information.
Cross-site scripting attacks may cause great damages. So be careful and be sure before you try xss payloads.
Thanks for reading. Have a nice day.
In every website I enter, I try XSS Payloads to an input place. Just curiosity. So what's XSS?
Cross-site scripting is one of the most common and well known vulnerabilities contained within web applications. It every year appears in the OWASP list of the Top Web Application Security Risks. According to some pages, XSS vulnerabilities are the most common vulnerability type discovered in bug bounty programs, despite the fact that most companies undervalue it because it rarely leads to large-scale data breaches.

The root cause of XSS vulnerabilities is when a web application uses untrusted input without performing proper validation first. If a web server embeds user input in a pages HTML code before sending it to the client, then malicious input could enable the execution of attacker-controlled code within the users browser. You need to filter inputs to prevent these attacks.
The reason for this is that the HTML standard allows other types of code to be embedded in HTML files if they are properly tagged. This includes Javascript code if it is contained within <script></script> tags. If an attacker provides malicious input that results in a valid web page when embedded in the HTML file, then the browser requesting the page will run the code believing that it is a legitimate part of the web page.
Different Types Of XSS
- Non-persistent (reflected)
- Persistent
- Server-side versus DOM-based vulnerabilities
- Self-XSS
- Mutated XSS (mXSS)
Most used types are Reflected XSS and Persistent, Stored XSS Attacks
Reflected XSS Attacks
Reflected attacks are those where the injected script is reflected off the web server, such as in an error message, search result, or any other response that includes some or all of the input sent to the server as part of the request. Reflected attacks are delivered to victims via another route, such as in an e-mail message, or on some other website.
Persistent XSS Attack
Persistent attacks are those where the injected script is permanently stored on the target servers, such as in a database, in a message forum, visitor log, comment field, etc. The victim then retrieves the malicious script from the server when it requests the stored information.
Cross-site scripting attacks may cause great damages. So be careful and be sure before you try xss payloads.
Thanks for reading. Have a nice day.







