What is Broken Authentication Vulnerability?
Broken Authentication is an authentication system vulnerability that allows a hacker to enter the web page unpermitted. So it is a vulnerability that allows a hacker to impersonate a user on a web page. It kind of resembles CSRF and they actually look alike. To exploit this vulnerability, hackers implement strategies that attempt to capture the user's credentials. These credentials are actually the user's login information (username and pass), but it would be a shame to call them just username and pass. Web applications use sessions and credentials to identify users. When it comes to the malfunction of this mechanism, this weakness occurs and hackers can log in as a different user.

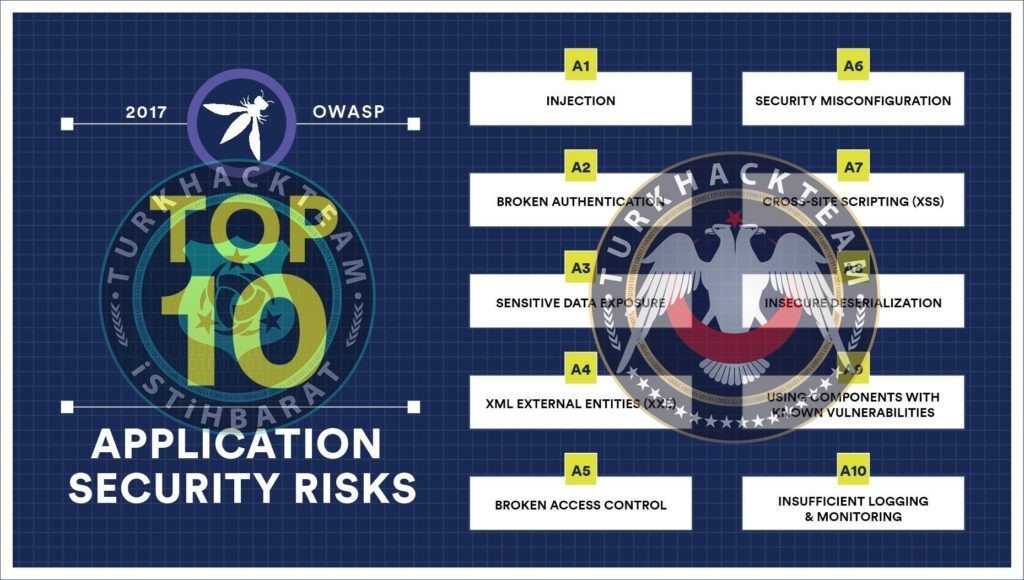
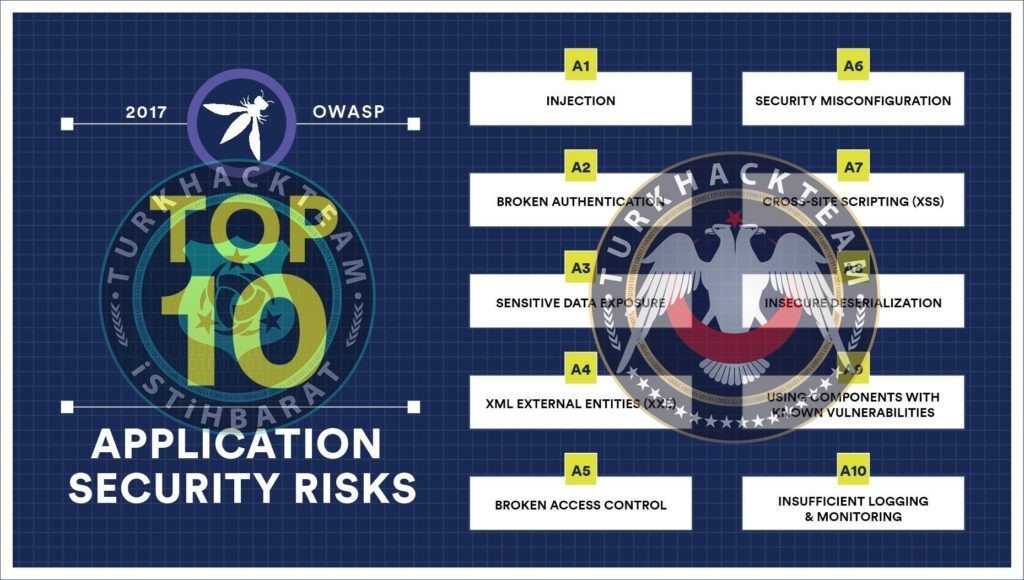
Among The Riskiest Vulnerabilities By OWASP
It can be said that the seriousness of the vulnerability was noticed late. But when it was noticed, security experts stated the fact that this vulnerability was a very sneaky and undetected threat. OWASP has added this vulnerability among the ten most risky (top 10) vulnerabilities.
User Risks
We will talk about the risks of users who have a membership in a place where the vulnerability is available. One of the biggest risks can be exposure to Credential Reuse attack. Users do not use different passwords on each platform. Hackers can use and sell the information they get through these vulnerabilities in botnets. A Credential Reuse attack is a typical brute-force attack that tries a user's password on one platform on different platforms.

How to avoid this exploit?
There are many ways to prevent this vulnerability, and most of them depend on session security. These methods are;
>> To keep session management up to date.
>> Using the Multi-Factor Authentication (MFA) systems.
>> Using a system that does not allow weak passwords.
>> Passwords in clear text (dB)
>> System to delete old session session_regenerate_id(true)

What is an MFA System?
A tool for user authentication. Aka The two-factor authentication process.

Deletion of the old Session
This is a software security precaution. A cookie is kept when the user logs in to the Web page. A system that will delete the old session when the user logs in again with authentication one day.

How do users protect themselves?
Being in places where this vulnerability is available consumes a great risk for users. It is up to users to protect themselves from these risks. Users should use two-factor authentication. Users' passwords should be strong and the same password should not be used everywhere. You can write down your passwords on a piece of paper. They can change your password via a link, and the best precaution against this is to be on reliable platforms and pay attention to incoming links, that is, in text. It may not be safe to use the remember me system.
Broken Authentication is an authentication system vulnerability that allows a hacker to enter the web page unpermitted. So it is a vulnerability that allows a hacker to impersonate a user on a web page. It kind of resembles CSRF and they actually look alike. To exploit this vulnerability, hackers implement strategies that attempt to capture the user's credentials. These credentials are actually the user's login information (username and pass), but it would be a shame to call them just username and pass. Web applications use sessions and credentials to identify users. When it comes to the malfunction of this mechanism, this weakness occurs and hackers can log in as a different user.

Among The Riskiest Vulnerabilities By OWASP
It can be said that the seriousness of the vulnerability was noticed late. But when it was noticed, security experts stated the fact that this vulnerability was a very sneaky and undetected threat. OWASP has added this vulnerability among the ten most risky (top 10) vulnerabilities.
User Risks
We will talk about the risks of users who have a membership in a place where the vulnerability is available. One of the biggest risks can be exposure to Credential Reuse attack. Users do not use different passwords on each platform. Hackers can use and sell the information they get through these vulnerabilities in botnets. A Credential Reuse attack is a typical brute-force attack that tries a user's password on one platform on different platforms.

How to avoid this exploit?
There are many ways to prevent this vulnerability, and most of them depend on session security. These methods are;
>> To keep session management up to date.
>> Using the Multi-Factor Authentication (MFA) systems.
>> Using a system that does not allow weak passwords.
>> Passwords in clear text (dB)
>> System to delete old session session_regenerate_id(true)

What is an MFA System?
A tool for user authentication. Aka The two-factor authentication process.

Deletion of the old Session
This is a software security precaution. A cookie is kept when the user logs in to the Web page. A system that will delete the old session when the user logs in again with authentication one day.

How do users protect themselves?
Being in places where this vulnerability is available consumes a great risk for users. It is up to users to protect themselves from these risks. Users should use two-factor authentication. Users' passwords should be strong and the same password should not be used everywhere. You can write down your passwords on a piece of paper. They can change your password via a link, and the best precaution against this is to be on reliable platforms and pay attention to incoming links, that is, in text. It may not be safe to use the remember me system.
Moderatör tarafında düzenlendi: