- 8 Nis 2020
- 221
- 73
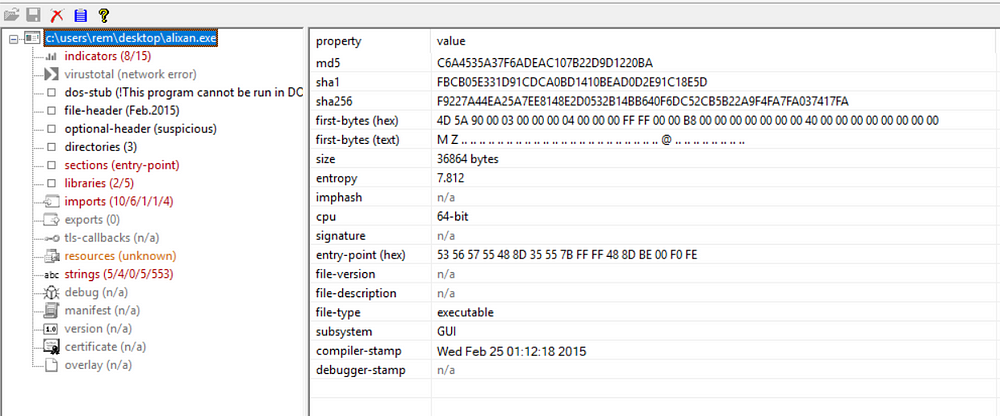
Packed Malware Detection
- Malware authors often seek to protect their creations from anti-malware products and from the tools that analysts use to examine malicious programs. They often accomplish this by using tools known as packers.- Packers are tools that compress, obfuscate, encrypt, or otherwise encode the original code
- The packed program decodes the code into memory when it runs
- This safeguards the specimen from static analysis techniques
- Packed programs are also difficult to disassemble and debug
- Not all malware is packed
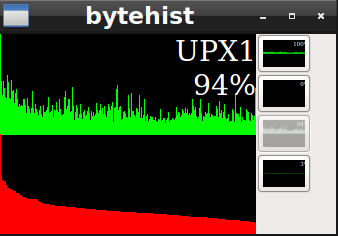
UPX — Ultimate Packer for eXecutables
- open source and common and simpler to open.
- Then we click on the section tab from the application tabs.
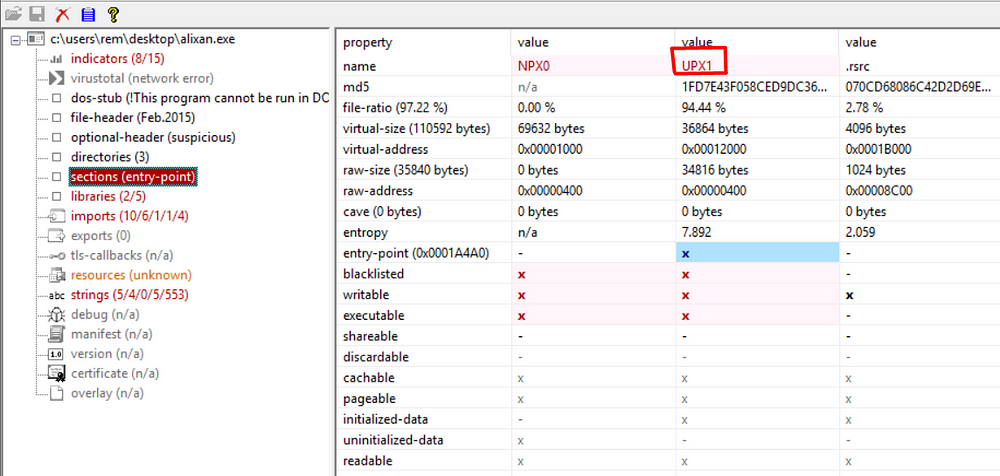
- As you can see, it indicates that our PeStudio file is packed on the UPX packer side.
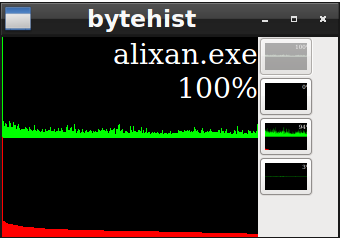
- Another way to assess the likelihood that a Windows executable might be packed is to examine the distribution of the file’s byte values. One tool that enables you to do this in a visual manner is Bytehist.Now we can try this
- Bytehist generates byte-usage histograms, showing you the frequency with which each byte value occurs in the file.
Command :
bytehist alixan.exe