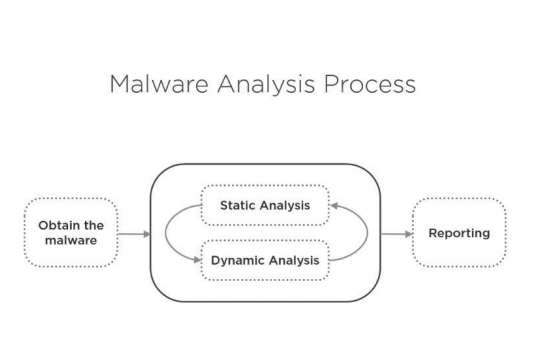
MALWARE ANALYSIS PROCESS
The malware analysis process can usually be divided into two main classes.
First, static analysis, second, dynamic analysis.
The first step is to identify the bad software and the last step is to report it.

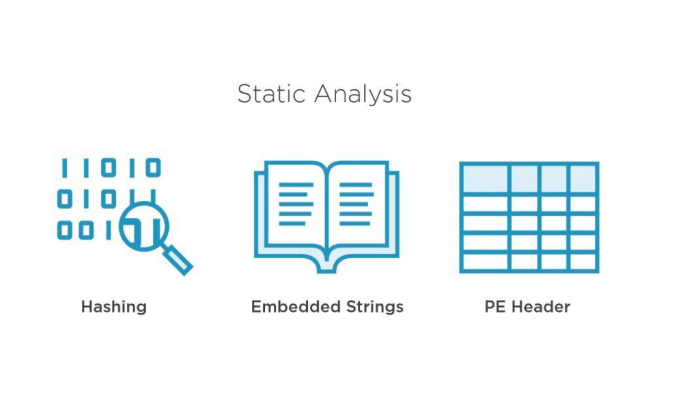
Static analysis involves three things;
Cryptological ciphers, embedded formations, the content of a behavior.
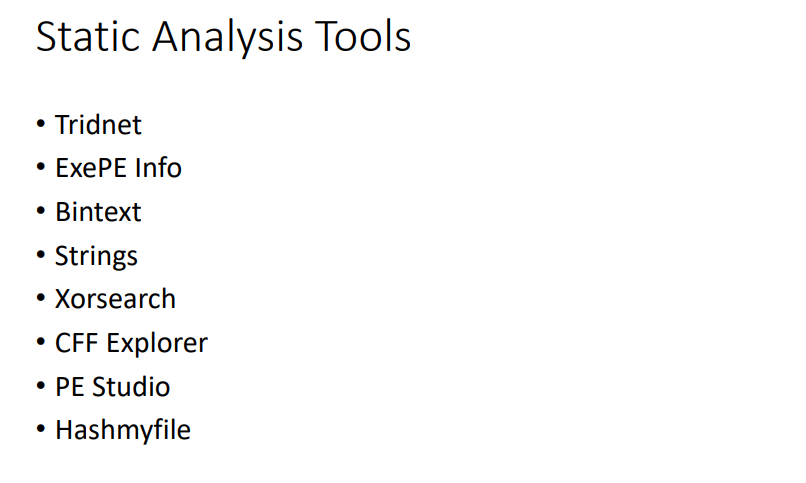
Statitic analysis tools are şekildedir.biz here we will use tridneti and pestudio.
Dynamic analysis consists of two parts, which are subdivided into two parts;
the first is taking a screenshot and the other is behavior monitoring.

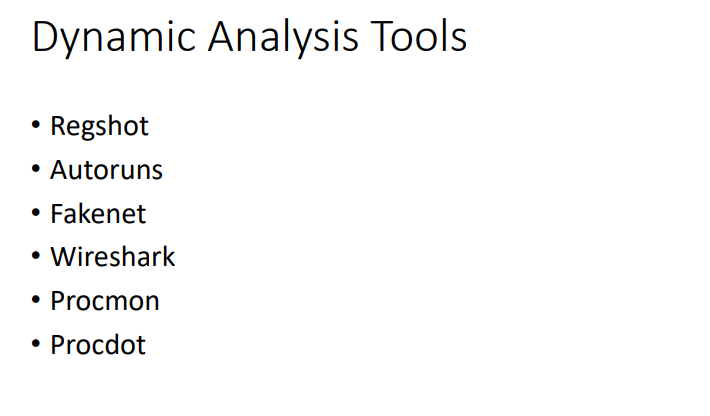
Dynamic analysis tools;
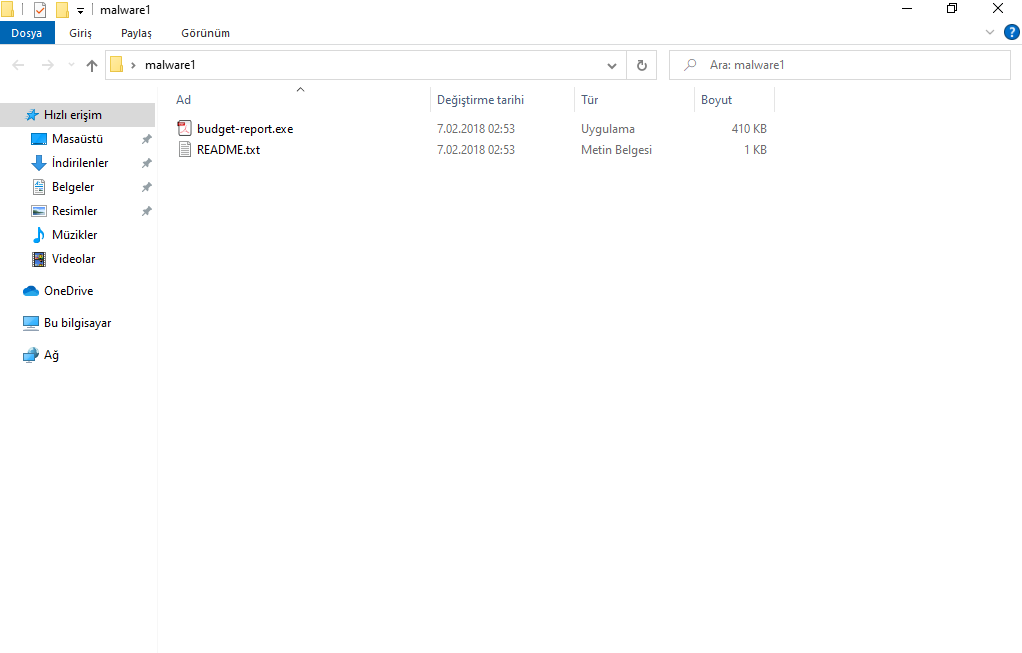
We open our folder our file in the folder is a .exe file with a PDF image Our first suspicion starts here.

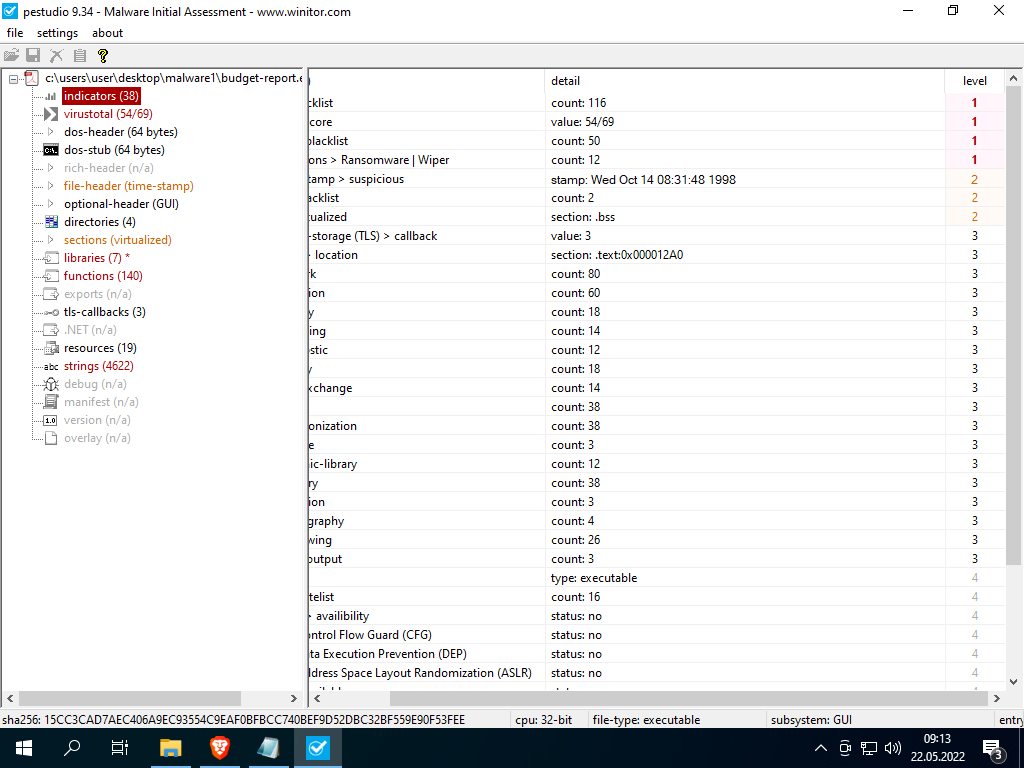
We reflect our file pestudio in the criteria here 1: Very dangerous 2: Medium 3: We see the low hazard classification in the indicators section;
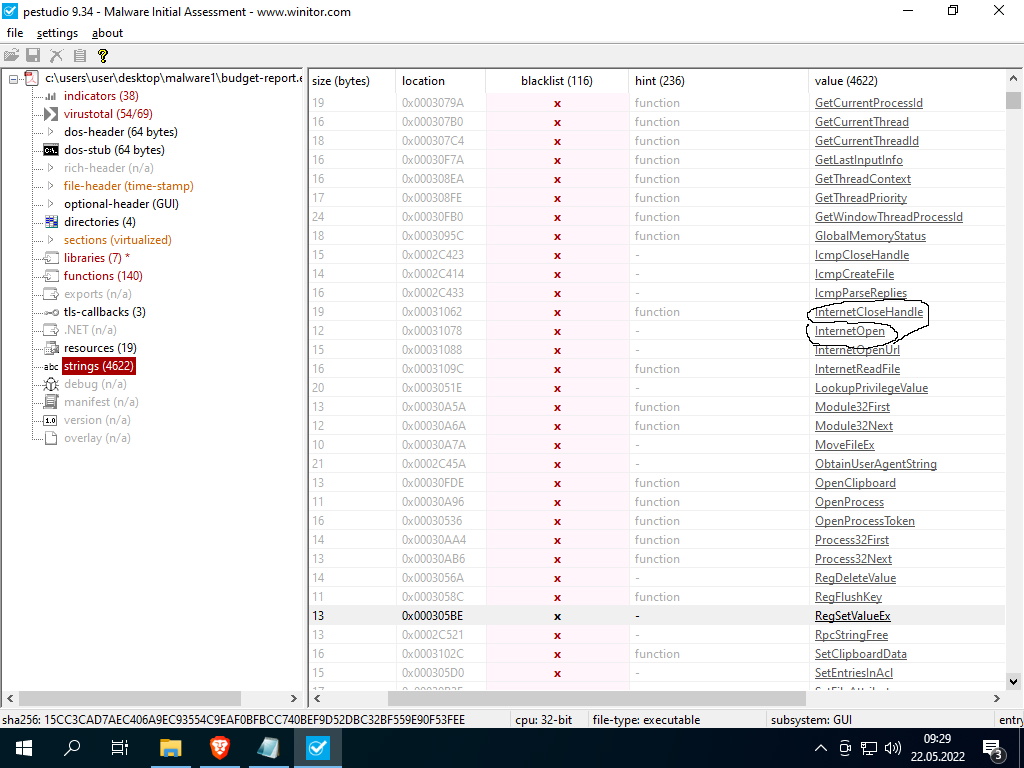
In the string category, some values catch my eye.
regsetvalue.exe: ften used for persistence in bad software
Post:Sending something to the Internet
Createtools32snapshoot:Taking snapshots
That's enough evidence, but let's examine other categories as well.

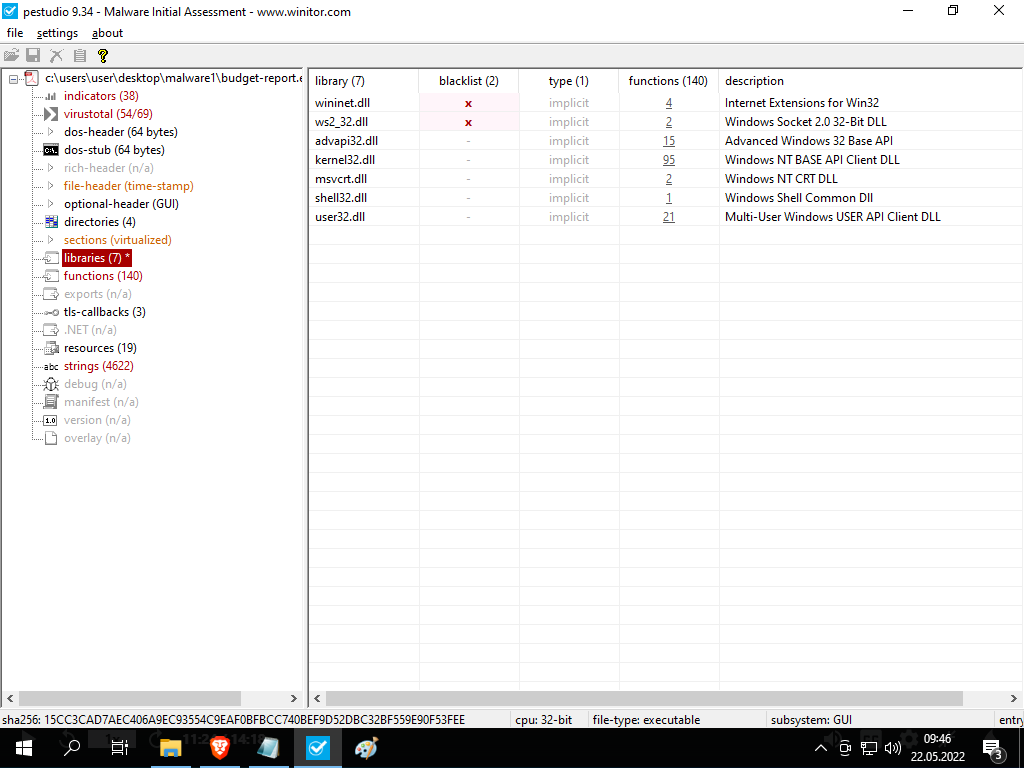
Here in the libraries section
Ws2_32.dll : used for internet connection bridge
User32.dll: Used for user interface;

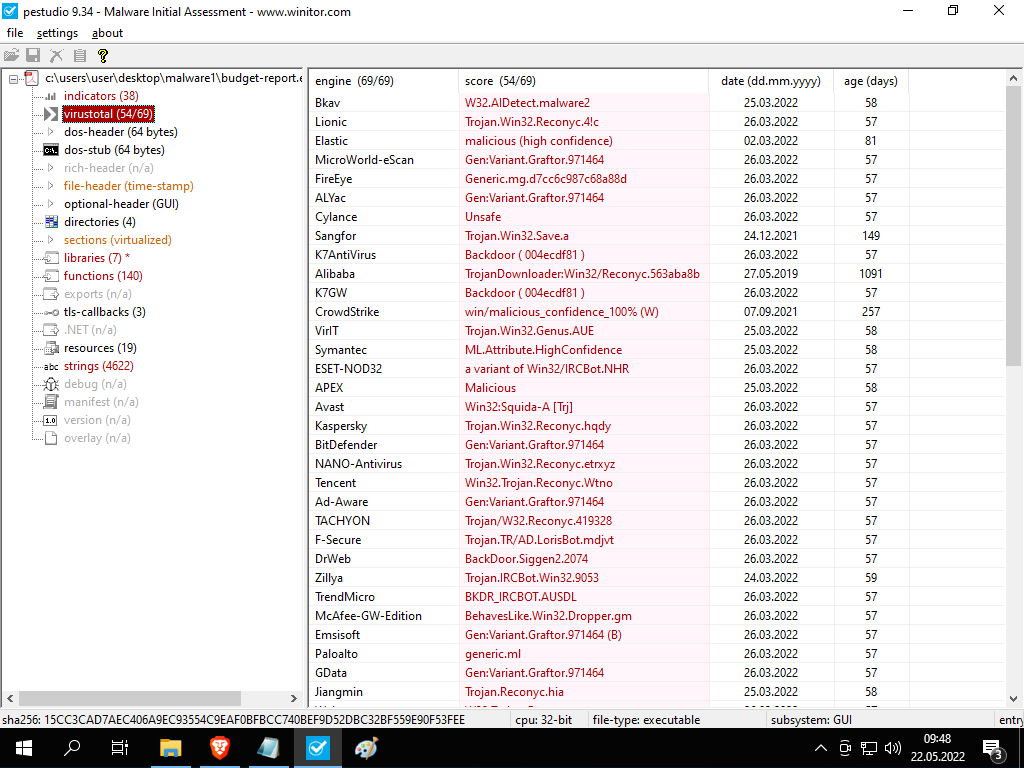
Since the virus has been caught in total results, our file has been confirmed to be a malicious software

Translator: @ByFelez
Subject Author: @Cakky
Subject: https://www.turkhackteam.org/konular/statik-ve-dinamik-analiz-kavrami-malware-sample-1-lab.2016662/