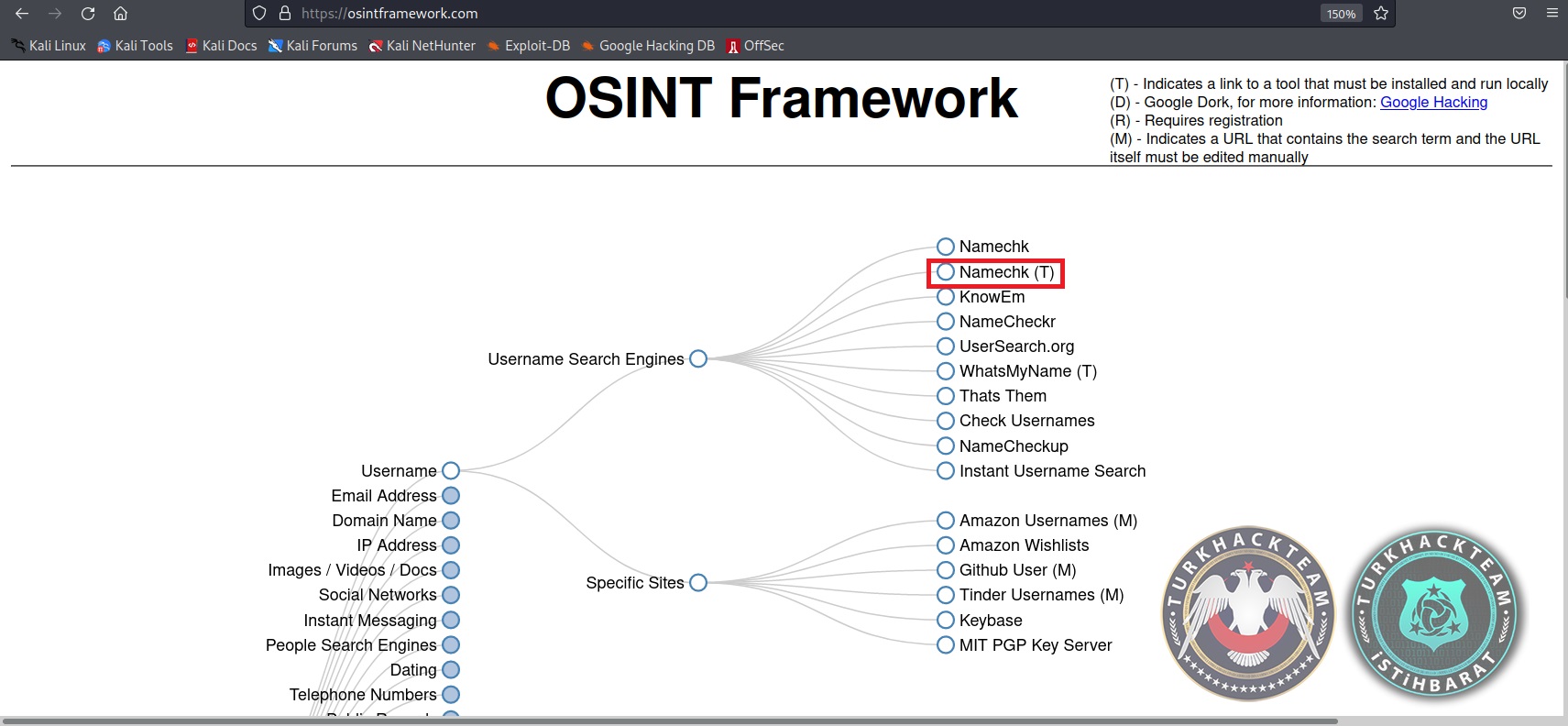
Osintframework – Usernames
Namechk – Namechk (T)
What is OSINT?
Today we will talk about Osintframework – usernames, one of the open source intelligence tools, our goal is to increase the resources we have and compare data from multiple sources with each other and come to a conclusion.
Before talking about osintframework – usernames, I would like to briefly touch on the topic of OSINT. OSINT, which we have heard a lot about as Open Source Intelligence, stands for "open source intelligence –open source intelligence" is actually an important preliminary step. Open Source Intelligence is an intelligence mechanism obtained by passing through a filter that decides whether "information that does not require confidentiality, is publicly available, collected for a specific purpose" is of an intelligence nature.
According to the US Department of Defense, OSINT is generated from publicly available information that is collected, used and distributed to an appropriate audience in a timely manner to meet a specific intelligence requirement.
From our social media posts to TV, Radio and periodicals, penetration tests with this analysis, attacks by professional attackers, etc., OSINT has been developed. it covers data that is open on the Internet up to. Collecting information about the target in studies is a passive information collection process that includes all stages of determining the connections established by the target.
OSINT consists of information with a basic structure. All the data from the content we share over the Internet to our likes and comments ensure the formation of OSINT. Thanks to the ease of information sharing and the speed of information dissemination on the Internet, every connection we make and every trace we leave constitutes OSINT. The collection of this information is legal. It is important that there is no communication with the target that will create an anomaly. The more information is collected about the target system or person,
in the later stages, it is possible to move so comfortably.
INFORMATION ACCESSIBLE WITH OSINT TOOLS
Due to the fact that most OSINT tools are free, it does not require a high budget at the information collection stage and reduces the cost. Since there is no direct contact with the target, it does not require the need for protection in terms of privacy and security. Therefore, it saves time on penetration tests. Information can be collected from different areas on the target with OSINT tools. Internet browsing related to the target can be done. (Bing, Google, Yahoo, Linkedin, DuckDuckGo, social media accounts, etc...) DNS records of the target can be detected. The IP addresses of the target can be detected. (subdomains, open ports, services, etc.) E-mail accounts belonging to the target can be identified. Technology infrastructures can be identified in target applications. (Every application detected here is very important. If there is a detected vulnerability in the applications used, the target system can be easily accessed through this vulnerability. Therefore, the definitions of the programs used and the current versions are important.). Metadata analysis (image, photo, video, location, API Key information, information leaked to the Internet) can be performed.
OSİNT HANDBOOK 2020
USERNAME CHECK
Namechk – Namechk (T)
What is OSINT?
Today we will talk about Osintframework – usernames, one of the open source intelligence tools, our goal is to increase the resources we have and compare data from multiple sources with each other and come to a conclusion.
Before talking about osintframework – usernames, I would like to briefly touch on the topic of OSINT. OSINT, which we have heard a lot about as Open Source Intelligence, stands for "open source intelligence –open source intelligence" is actually an important preliminary step. Open Source Intelligence is an intelligence mechanism obtained by passing through a filter that decides whether "information that does not require confidentiality, is publicly available, collected for a specific purpose" is of an intelligence nature.
According to the US Department of Defense, OSINT is generated from publicly available information that is collected, used and distributed to an appropriate audience in a timely manner to meet a specific intelligence requirement.
From our social media posts to TV, Radio and periodicals, penetration tests with this analysis, attacks by professional attackers, etc., OSINT has been developed. it covers data that is open on the Internet up to. Collecting information about the target in studies is a passive information collection process that includes all stages of determining the connections established by the target.
OSINT consists of information with a basic structure. All the data from the content we share over the Internet to our likes and comments ensure the formation of OSINT. Thanks to the ease of information sharing and the speed of information dissemination on the Internet, every connection we make and every trace we leave constitutes OSINT. The collection of this information is legal. It is important that there is no communication with the target that will create an anomaly. The more information is collected about the target system or person,
in the later stages, it is possible to move so comfortably.
INFORMATION ACCESSIBLE WITH OSINT TOOLS
Due to the fact that most OSINT tools are free, it does not require a high budget at the information collection stage and reduces the cost. Since there is no direct contact with the target, it does not require the need for protection in terms of privacy and security. Therefore, it saves time on penetration tests. Information can be collected from different areas on the target with OSINT tools. Internet browsing related to the target can be done. (Bing, Google, Yahoo, Linkedin, DuckDuckGo, social media accounts, etc...) DNS records of the target can be detected. The IP addresses of the target can be detected. (subdomains, open ports, services, etc.) E-mail accounts belonging to the target can be identified. Technology infrastructures can be identified in target applications. (Every application detected here is very important. If there is a detected vulnerability in the applications used, the target system can be easily accessed through this vulnerability. Therefore, the definitions of the programs used and the current versions are important.). Metadata analysis (image, photo, video, location, API Key information, information leaked to the Internet) can be performed.
OSİNT HANDBOOK 2020
USERNAME CHECK
1) Aware Online: Username Search Gebruikersnamen search tool - Gebruik handige OSINT Tools
2) Check User Names CheckUsernames Searches 160 Social Networks - KnowEm.com searches over 500
3) GoFindWho https://gofindwho.com
4) Instant Username https://instantusername.com
5) IntelligenceX:Username Lookup Tools - Intelligence X
6) Investigo GitHub - tdh8316/Investigo:
7) KnowEm http://www.Knowem.com
8) leakpeek https://leakpeek.com
9) Loginella Unshort and check any short url
10) Lullar Lullar Com - Search People Profile by Email or Username
11) Maigret GitHub - soxoj/maigret:
12) Namecheck Username Checker - #1 Social Media Username Search Tool
13) Name Checkr namecheckr | Social and Domain Name Availability Search For Brand Professionals
14) Name Checkup NameCheckup - Find Available Username
15) Namechk http://www.namechk.com
16) Namechk (T) (app) GitHub - GONZOsint/Namechk: Osint tool based on namechk.com for checking usernames on more than 100 websites, forums and social networks.
17) Namech_k.sh GitHub - GONZOsint/Namechk: Osint tool based on namechk.com for checking usernames on more than 100 websites, forums and social networks.
18) Name Vine Instantly Find a Domain, Facebook & Twitter Account - Namevine
19) Neuskool neuskool.com / the personal start page
20) Peekyou Username Search | Find People by Username at PeekYou
21) Pipl https://pipl.com
22) Scylla GitHub - MandConsultingGroup/Scylla: The Simplistic Information Gathering Engine | Find Advanced Information on a Username, Website, Phone Number, etc.
23) Search POF SearchPOF.com - Search POF by Username
24) Sherlock GitHub - sherlock-project/sherlock:
25) Snitch.name snitch.name :: The Social White Pages
26) Snoop GitHub - snooppr/snoop: Snoop — инструмент разведки на основе открытых данных (OSINT world)
27) SocialPath GitHub - woj-ciech/SocialPath: Track users across social media platform
28) Social Recon GitHub - famavott/osint-scraper: Social Recon
29) socialscan socialscan
30) socid_extractor GitHub - soxoj/socid-extractor:
31) Sou o Cara Social Explorer
32) Spokeo Spokeo - People Search | White Pages | Reverse Phone Lookup
33) suIP.biz Бесплатный онлайн сервис по поиску пользователя в социальных сетях
34) Username Checker API Build, Collaborate & Integrate APIs | SwaggerHub
35) Userrecon GitHub - issamelferkh/userrecon
36) User Search http://www.usersearch.org
37) WhatsMyName (app) WhatsMyName Web
38) WhatsMyName GitHub - WebBreacher/WhatsMyName: This repository has the unified data required to perform user enumeration on various websites. Content is in a JSON file and can easily be used in other projects.
39) MediaMister Instagram Username Checker tool Instagram Username Availability Checker | Media Mister
Namechk
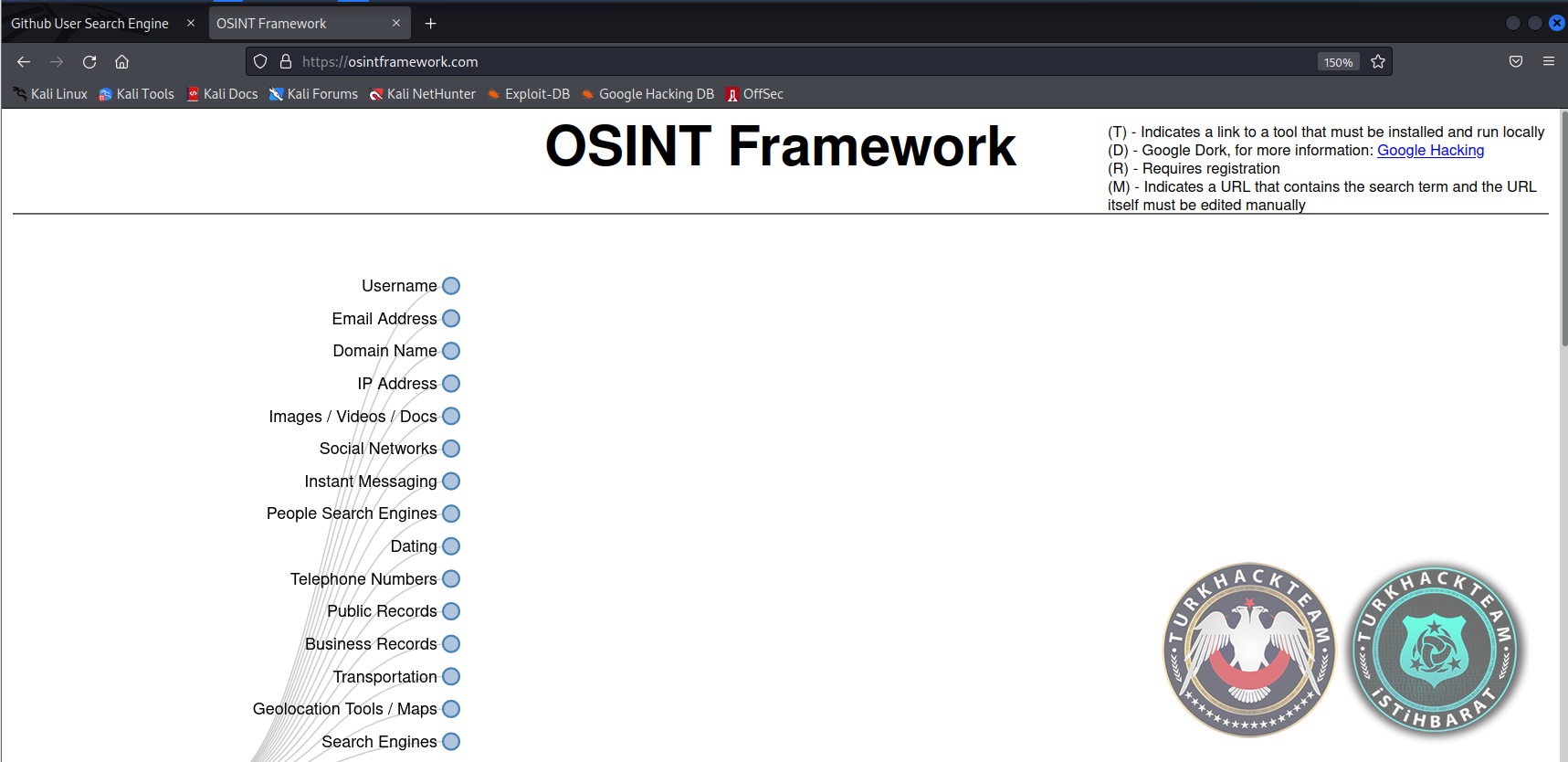
Osintframework.com I clicked on the *Username section of the site..
Then the *Username tab was divided into 2..
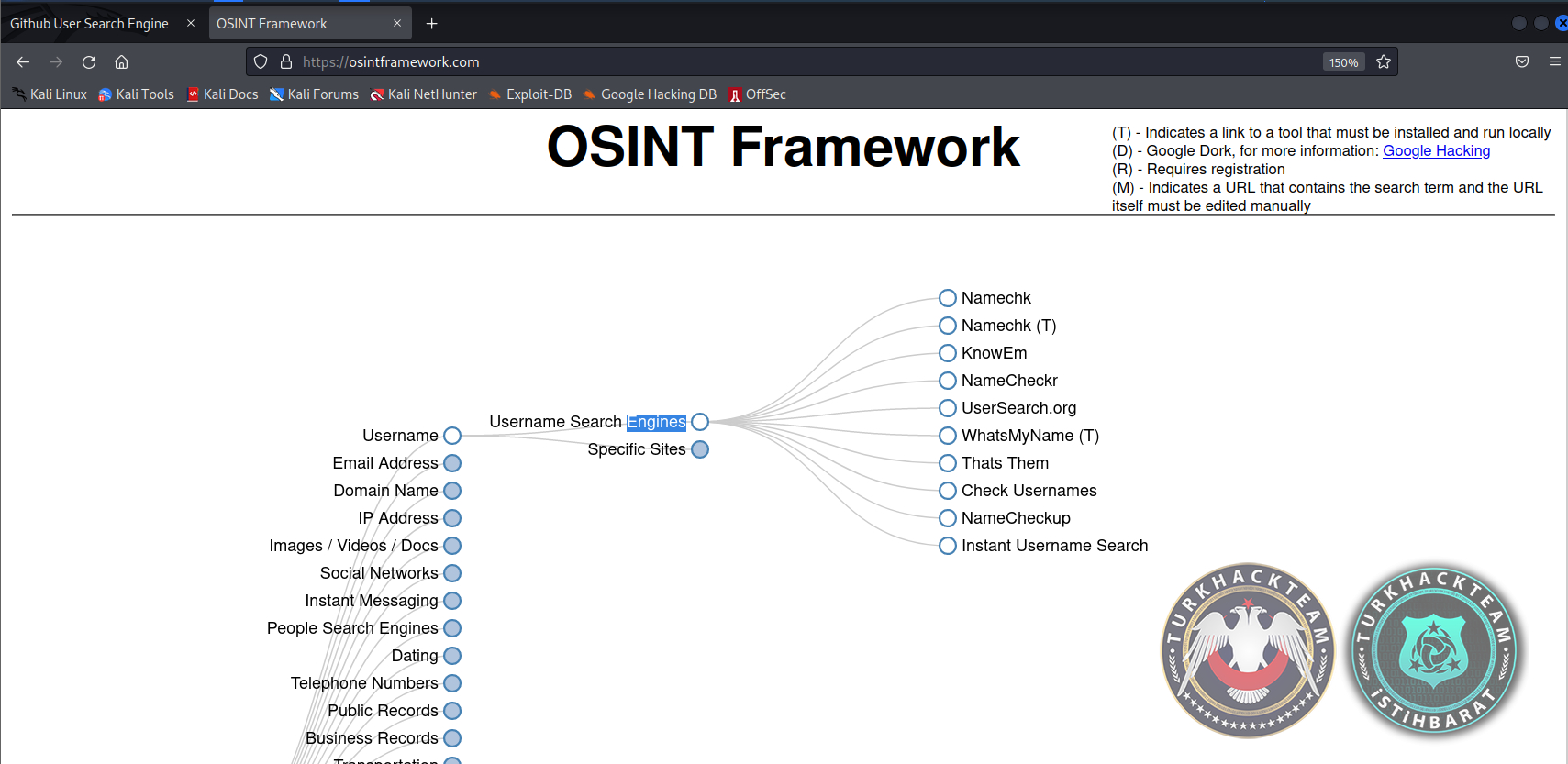
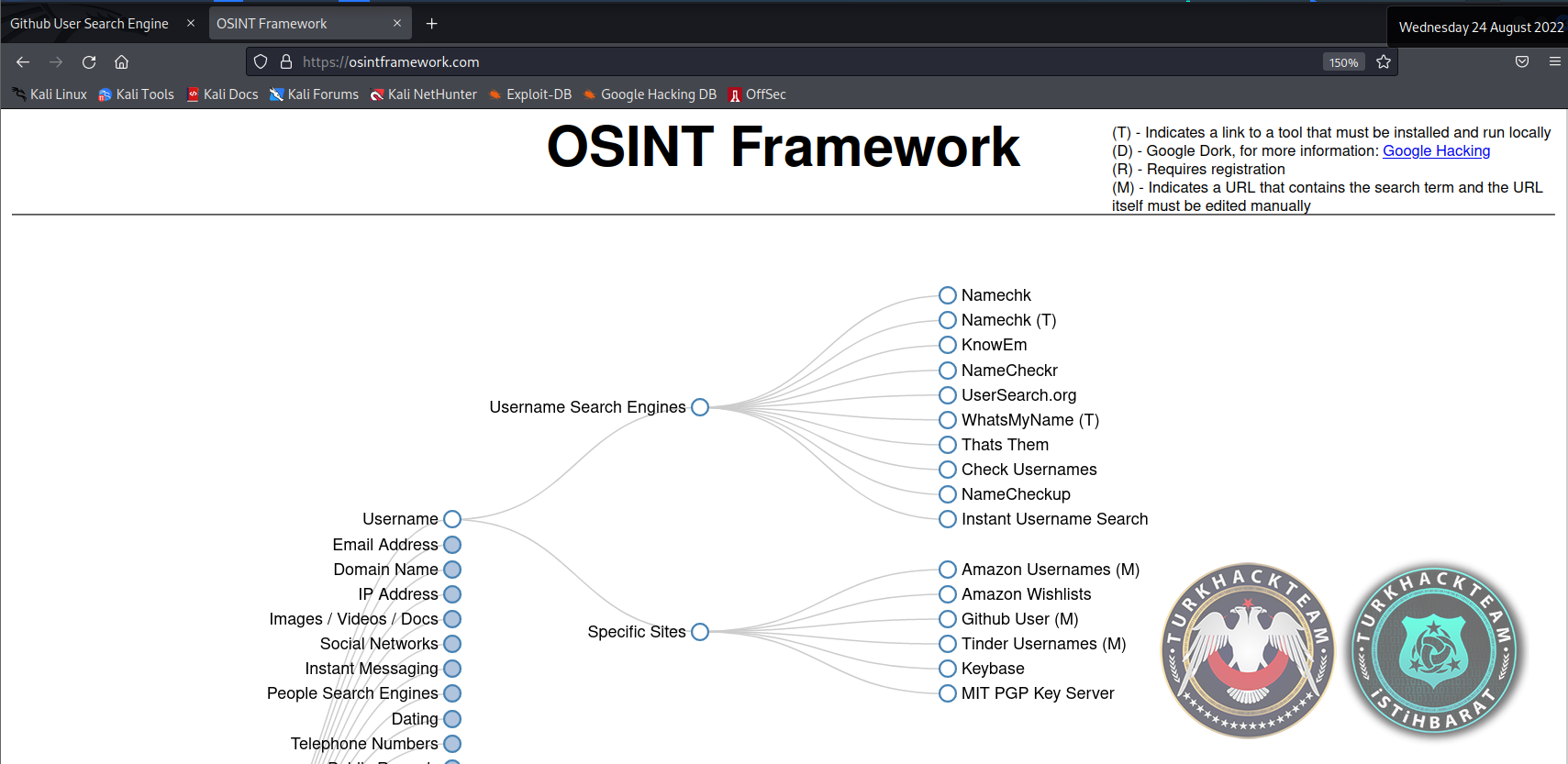
*Username Search Engines
*Specific Sites
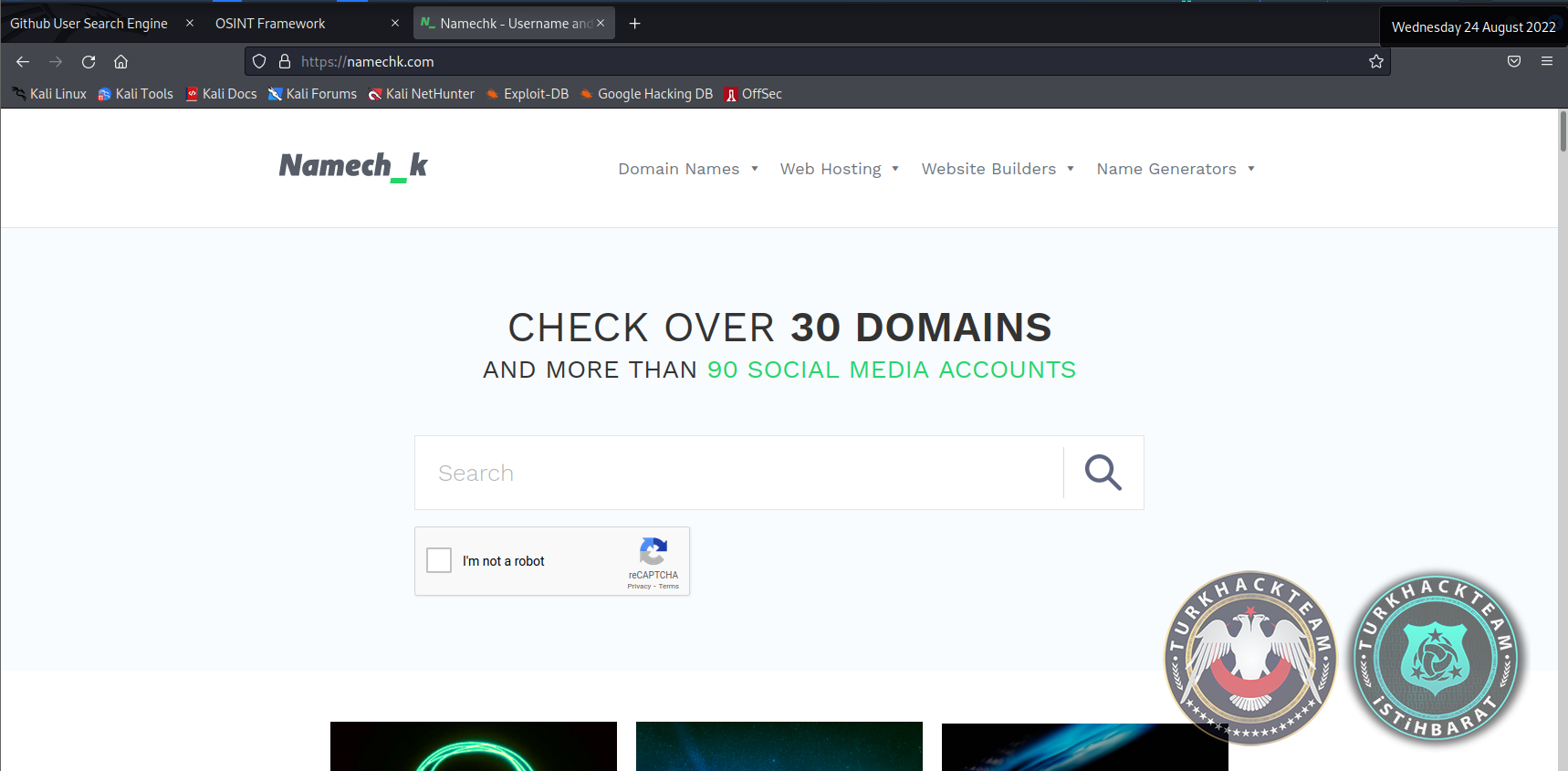
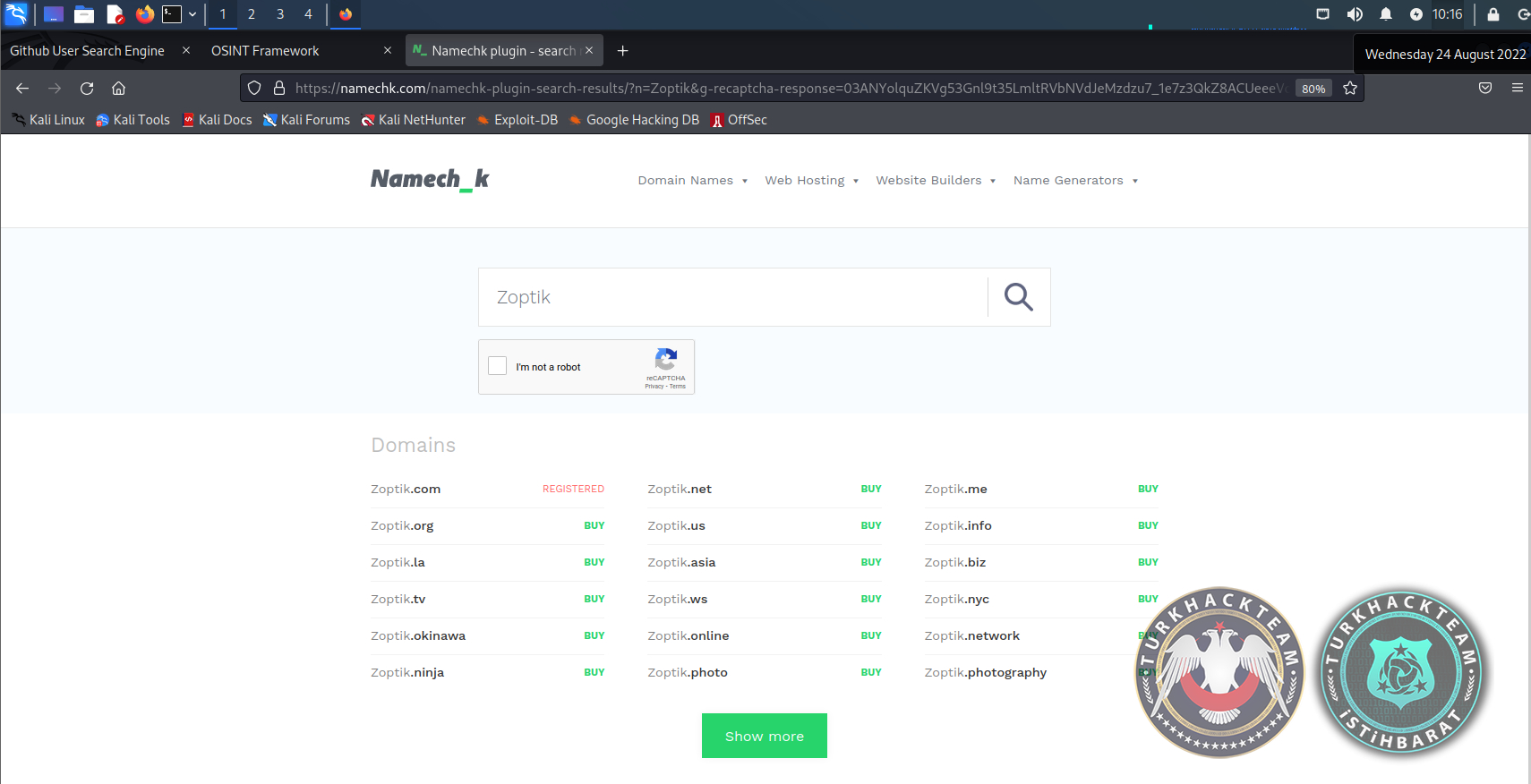
I entered the Namechk site at the top first.. It checked whether the connection is secure. Then came the website..
The top side of the Namechk Web page is the entire Namechk web page
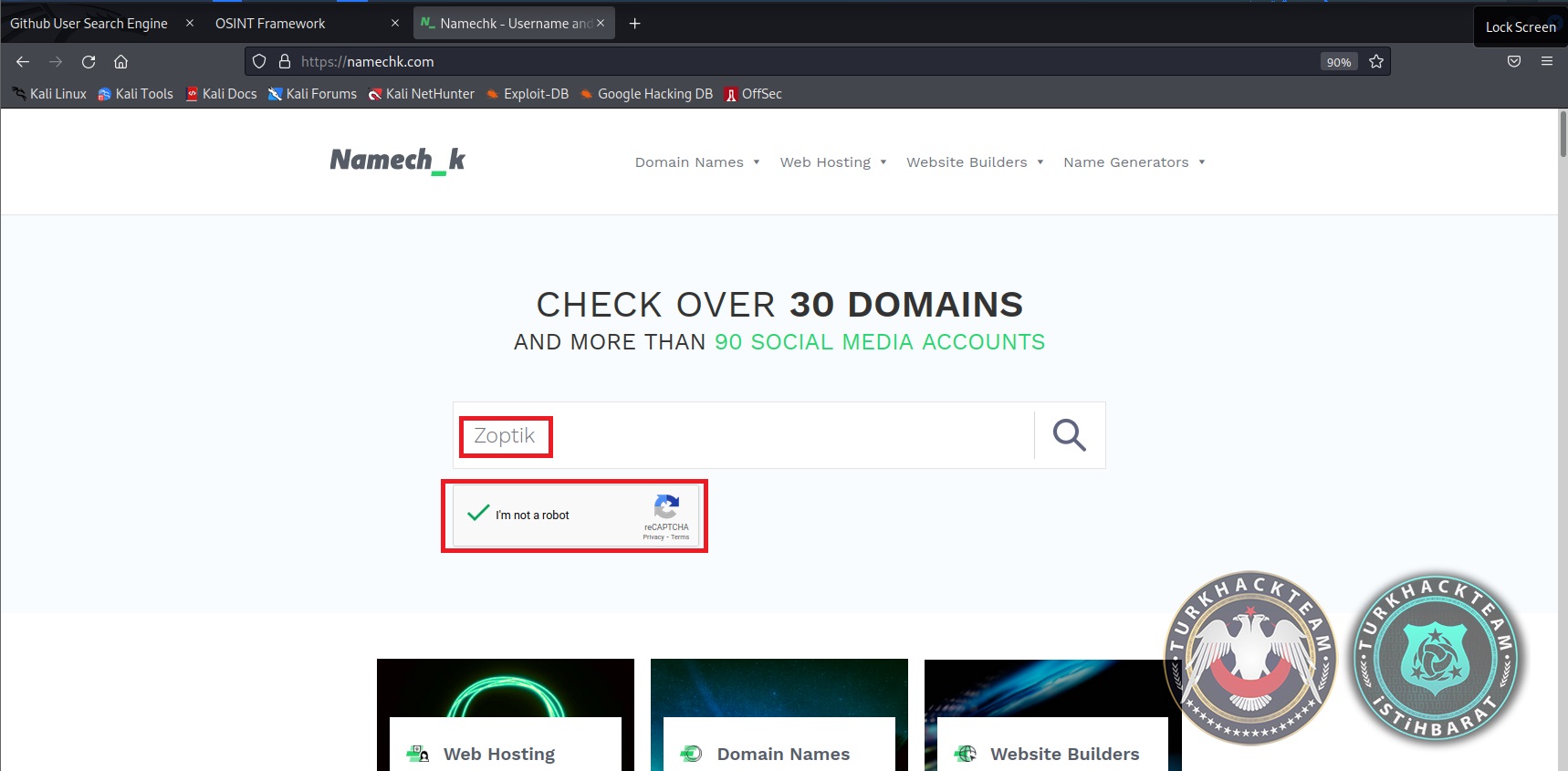
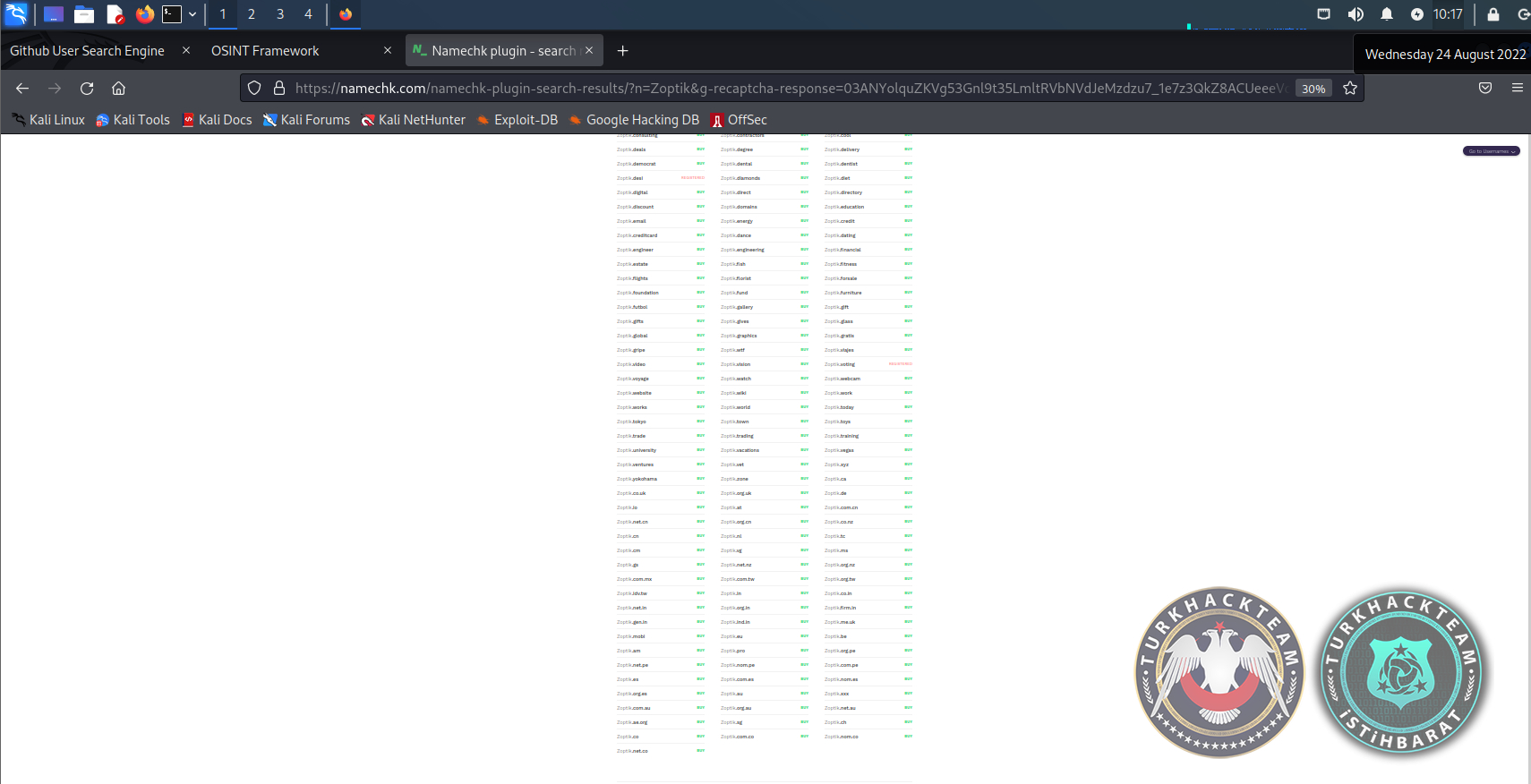
I wrote zoptik and marked capthcha.. then I clicked on the search icon, which is like a magnifying glass on the right side. Dec.. it removed the domains first..
There is another icon called “Show More” in green at the bottom. I clicked on that too..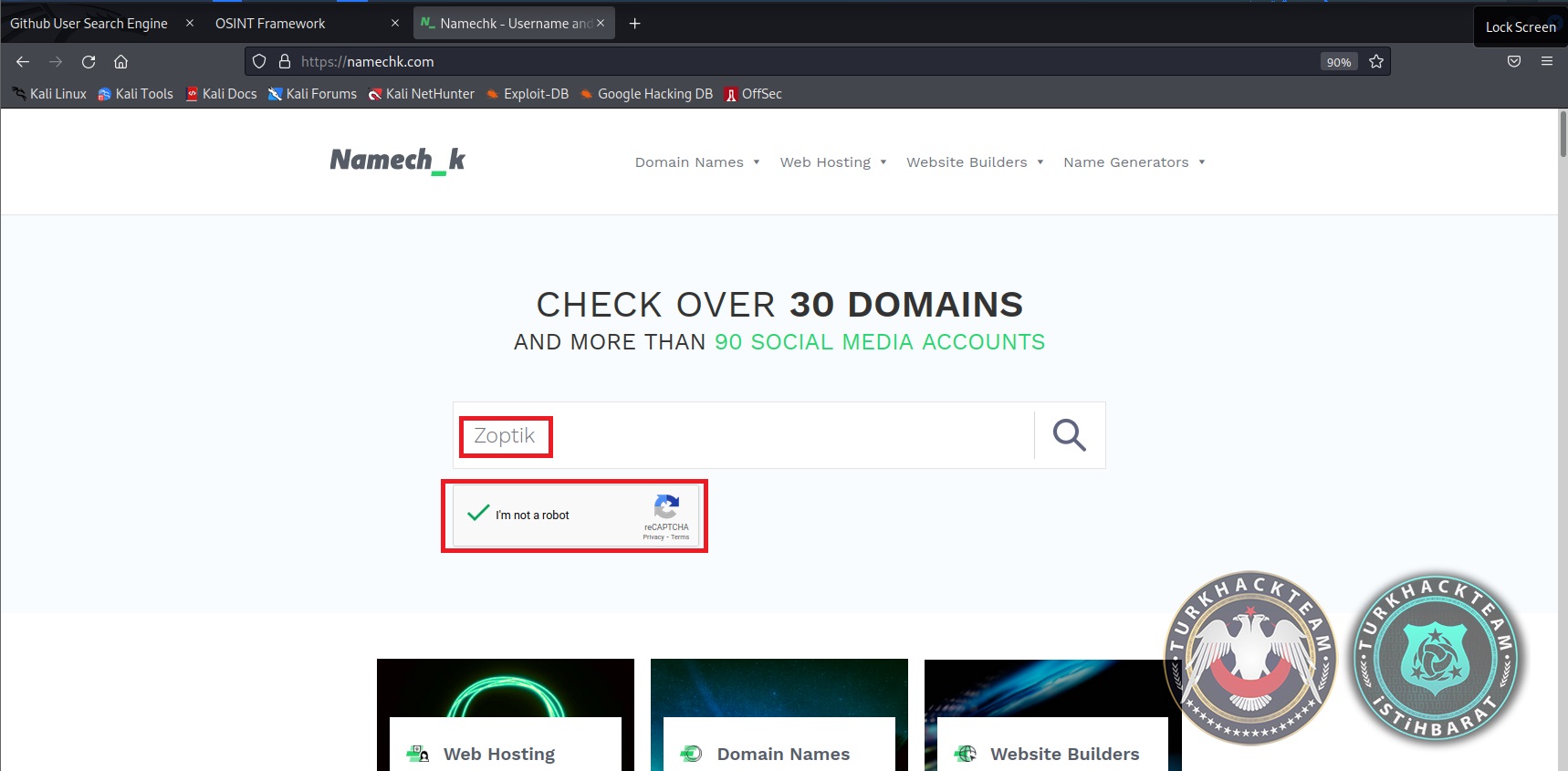
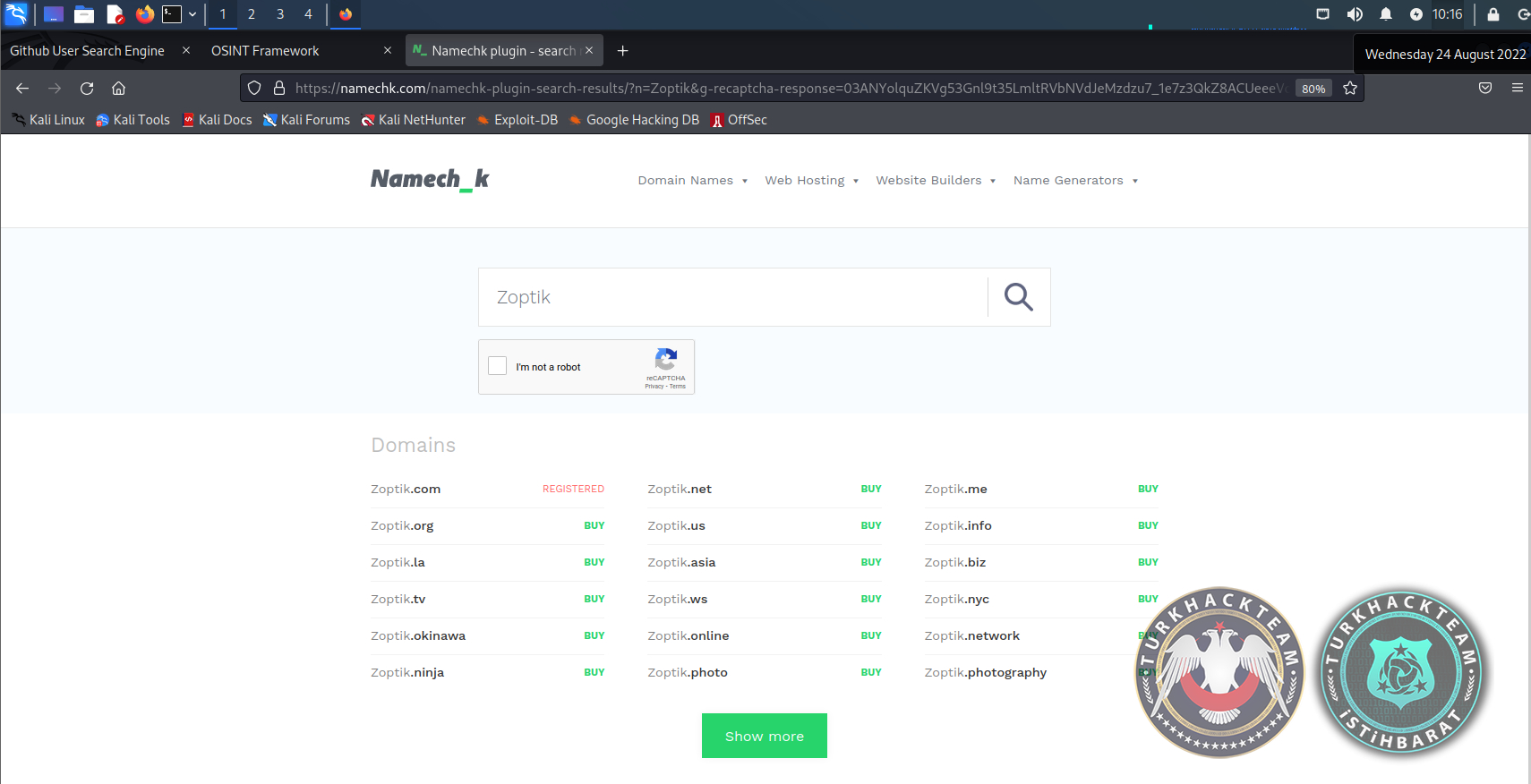
of these addresses, the red ones are used, and the green ones are unused domains.
We can also buy green domain names if we want.
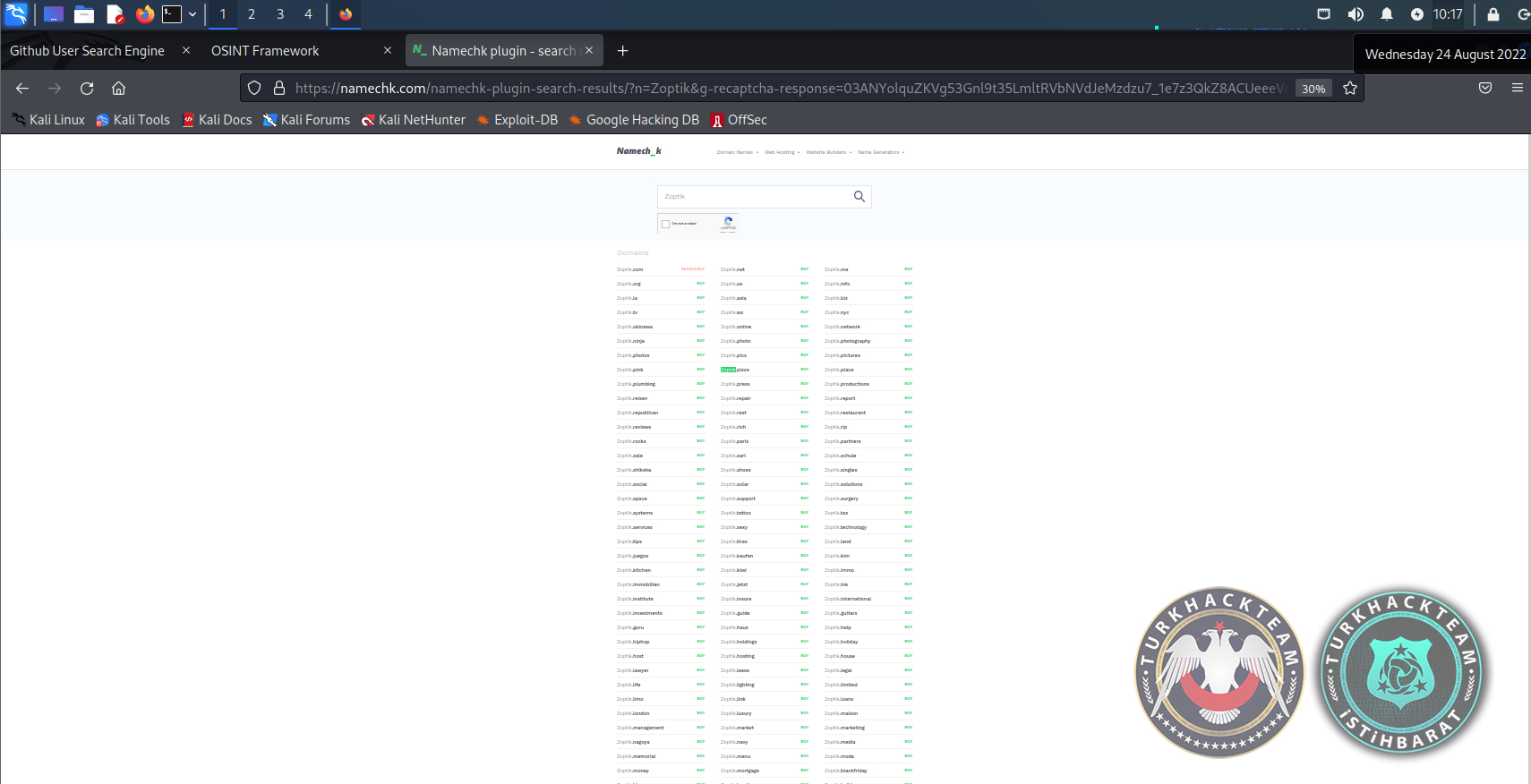
Later, I switched to “Zoptik” queries in usernames on social media.
The results are below..
The reds are again sites with the domain name ”Zoptik", the greens are sites without it.
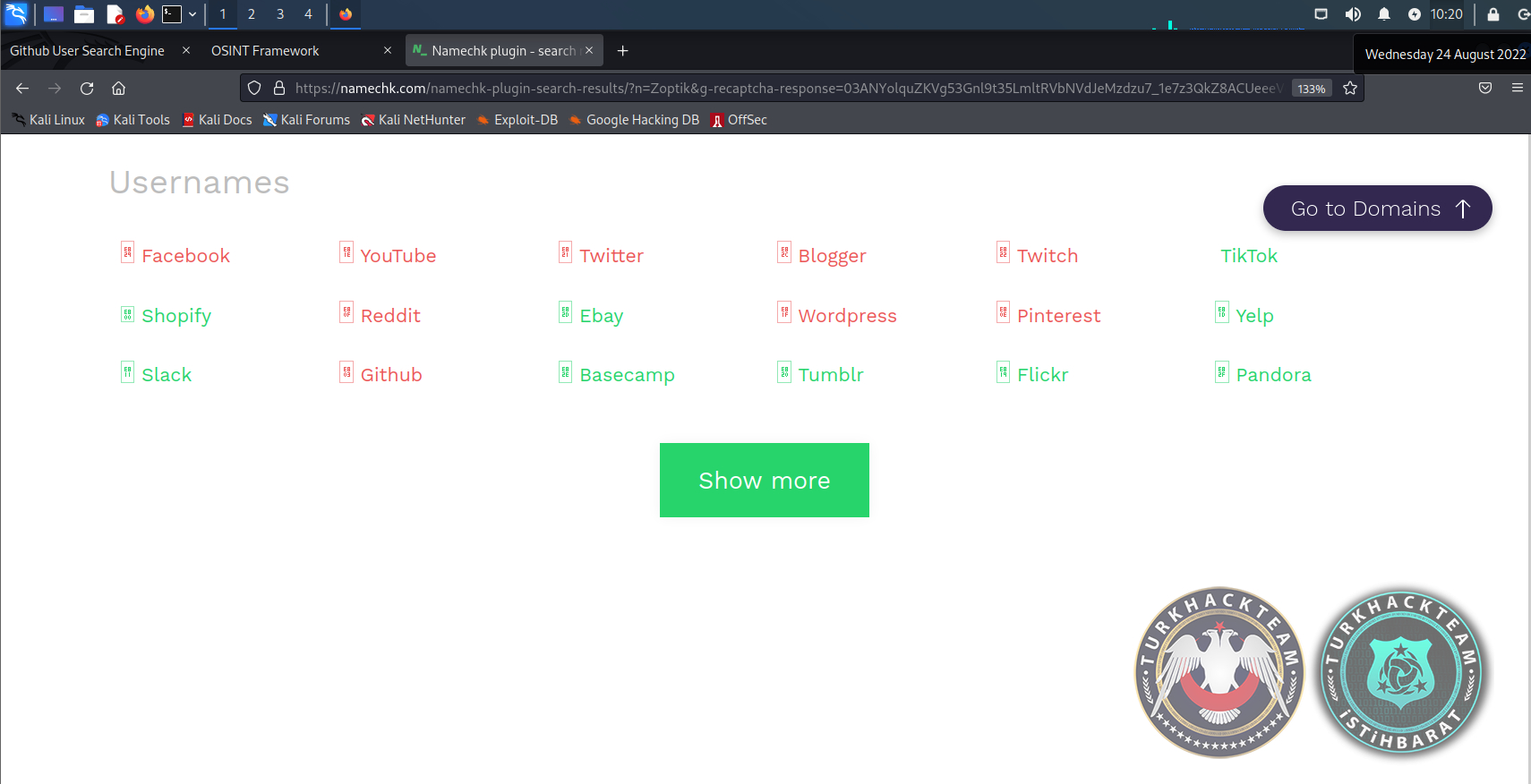
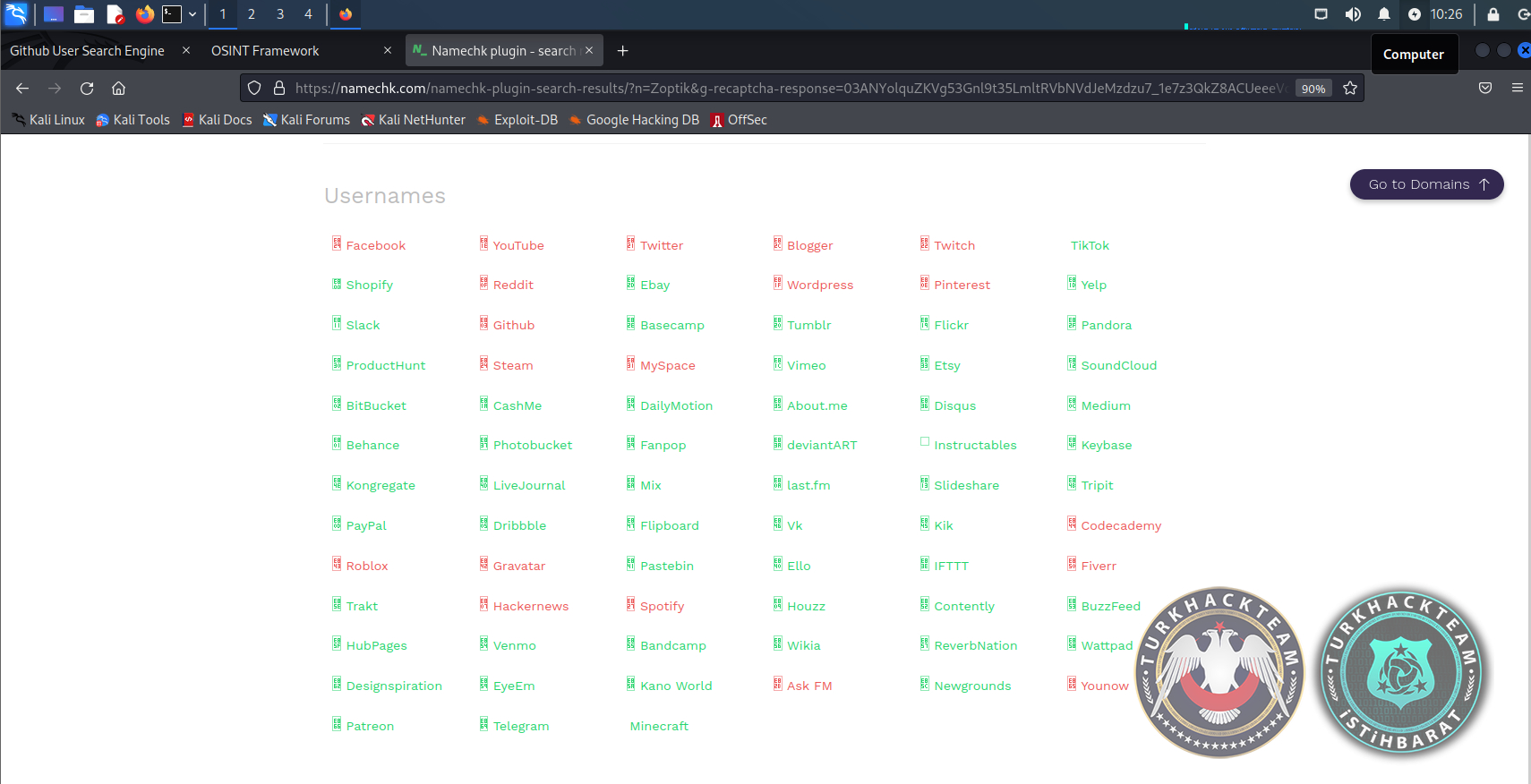
By clicking on “Show More” again, I got more results about the “Zoptik” query.
You can see the latest result above..:
Then I decided to get into one of these reds. I chose Wordpress, the login page came first.. After entering my own e-mail address and password, the site opened.. at this point, for example, I can crack my own password with a brute force attack.. Of course I'm not going to do that..However, by choosing the way to write my own email and password, I show myself to be an ethical hacker and enter my site..
Thus, the review of the Namechk site ends: In short, we can find out which domains the user names on this site have or not, which sites on social media are members or not, basically.. In addition, user accounts can even be hacked by brute force and social media accounts can be accessed.
_________________________________________________
Namechk (T)
Also namechk.com there is another link under his site called Namechk (T)..
this link is the link that connects the Namechk(T) in osintframework to the github application.
There is a namechk application in this github link.. But it's on github.the zip file does not work.
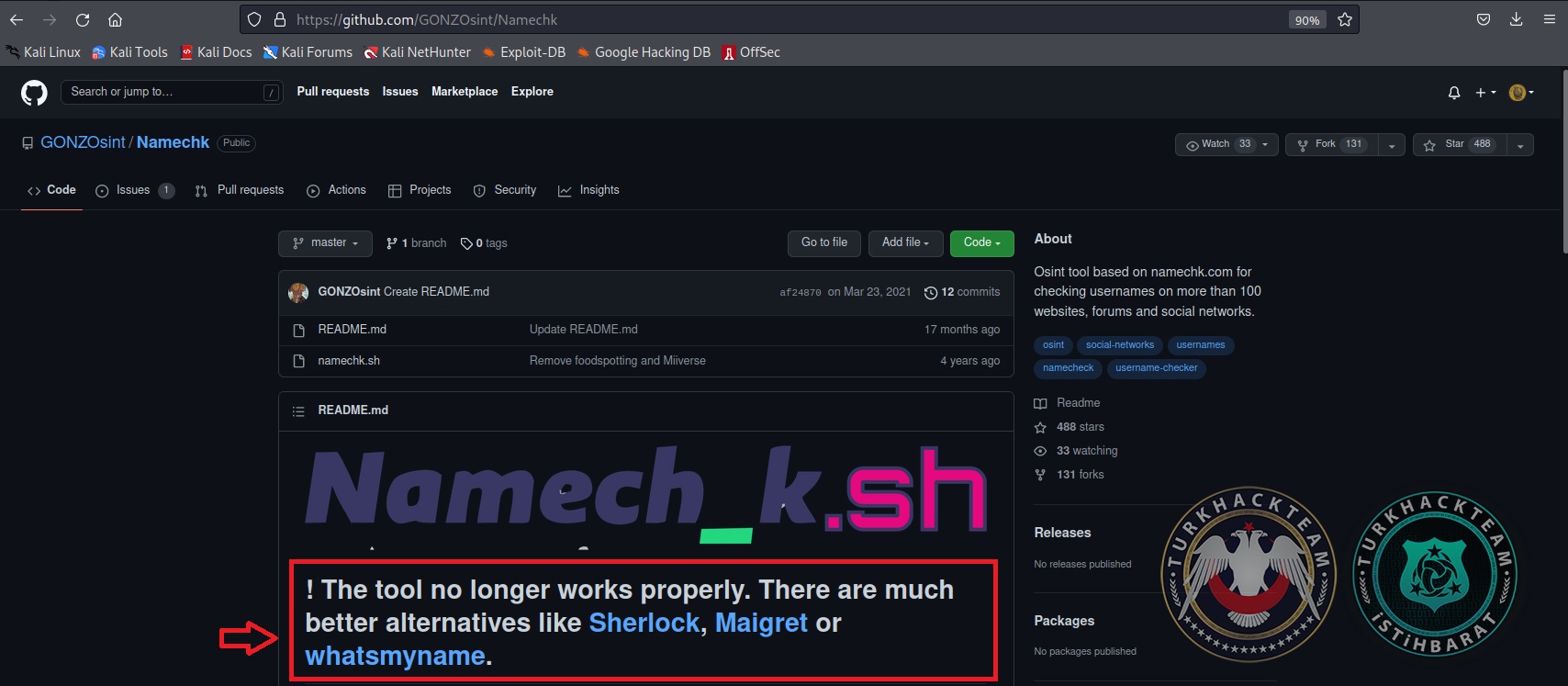
-This is the end of the site.-
Subject : https://www.turkhackteam.org/konular/osintframework-usernames-namechk-namechk-t.2022930/
subject owner : @Zoptik
the translator : @aleexb
Moderatör tarafında düzenlendi: